March 25, 2021
Updated April 19, 2021: We are adding several updates to this series of posts to reflect new events and new information that has become public just in the last few weeks. Each addition is labeled by the boldface word “UPDATE:” preceding the added paragraph.
I. introduction
Many of the posts on this site deal with the pseudoscience and disinformation that get spread when unintended global consequences of human-developed technology collide with the bottom-line interests of corporations and governments. The current post extends that theme to information technology, namely, to the unintended consequences of our rapidly growing reliance on computers and software to store our data, protect our secrets, communicate with friends and colleagues, pay our bills, and control our accounts, our elections and our infrastructure. Exploitation of flaws in the software and hardware on which that technology rests fuel cybercrime, cyber-espionage and cyberwar.
But in this case, we have to deal not so much with disinformation as with a paucity of information. The large software corporations and many industrial companies who have been subjected to massive hacking of one type or another have often been reluctant to publicize detailed information about those flaws and incidents. The players in the black market of buying and selling those exploits have little interest in going public. And the governments that wish to protect their ability to use such exploits for espionage and “warfare” are intent to keep details secret. We should clarify at the start that when we use the term “cyberwar” or “cyber warfare,” we are discussing attacks on other countries that take place in supposed “peacetime,” in the absence of any formal declaration of war, as well as “cold war” tactics with potentially devastating real-time consequences.
But in the new book This is How They Tell Me the World Ends: The Cyberweapons Arms Race, New York Times reporter Nicole Perlroth tells a compelling and terrifying story of the development of cyberweapons based on the still incomplete information she has managed to unearth through a decade of investigative journalism. The title of Perlroth’s book seems to be inspired by a quotation attributed to Nathaniel Borenstein, one of the two developers of the software to allow files to be attached to e-mail messages, a development now widely exploited for phishing scams: “The most likely way for the world to be destroyed, most experts agree, is by accident. That’s where we come in; we’re computer professionals. We cause accidents.”
Humans are imperfect and software developers are no exceptions. So, the occurrence of flaws in computer programs – errors in logic that can allow uninvited guests to burrow into, modify, corrupt, and even take over the workings of the program, often without detection – are at some level inevitable. But the frequency of occurrence of exploitable vulnerabilities has been enhanced by a business philosophy that incentivizes speed and disruption over care and accuracy. This philosophy is typified by Mark Zuckerberg’s admonition to Facebook staff to “Move fast and break things.” Developers of commercial software have traditionally been more focused on getting programs to perform the intended functions correctly than on making their code secure against unanticipated hacking attacks. It is only the worldwide proliferation of serious cybercrime, cyber-espionage and cyberwar attacks that has led the large software corporations to a belated emphasis on cyber-security. Perlroth reveals in her book that on a recent visit to the Facebook headquarters, she encountered graffiti on a wall that had featured Zuckerberg’s “Move fast and break things” mantra. The phrase had been crossed out, and in its place someone had written “Move slowly and fix your shit.”
Meanwhile, flaws that have not yet been patched or even detected, and patches that have not been adopted by commercial users of outdated software, are now widely and routinely exploited to steal proprietary information, to spy on citizens, to demand ransoms for “kidnapped” systems, to disrupt democratic elections, and to threaten the control apparatus for the technologies that govern so much of our lives and our infrastructure. The same flawed software is used in smart phones and computers worldwide, computers that often reside within large networks and are interconnected via internet access. The growing investment in the “Internet of Things” is rapidly expanding the diversity of devices and inter-device communications that are susceptible to infection.
Recent history has taught us that few, if any, systems are truly secure. New computer exploits have sometimes been implanted within smart phone apps, or software updates intended to patch previously identified flaws, or even through the anti-virus or anti-malware program updates used to protect your systems from infection. And a suitably designed exploit, once implanted in one system, can easily worm its way through networks and internet connections to infect vast numbers of computers.
The U.S., and specifically its National Security Agency (NSA), was once the only cyber superpower in the world, jealously guarding a secret stockpile of exploits, but that situation has changed rapidly. A thriving black market and massive hacks and leaks have provided worldwide access to computer exploits. So, potential exploiters and potential victims are now spread across the globe. Countries that could not afford to compete with the major powers in building conventional or nuclear warfare arsenals can easily purchase cyberweapons and set up hacking teams to use them against their enemies.
These developments have leveled the playing field in an ongoing cold war era of “mutually assured cyber-destruction,” in which various countries have implanted exploits to be activated later within controls for critical infrastructure in various other countries. These are the cyberweapons of mass destruction, the most likely instruments of 21st-century warfare. And the U.S. is more vulnerable to cyberwar attacks than most other countries, simply because a wider variety of systems and infrastructure are computer-controlled and networked in the U.S.
In this post, we describe some of the vulnerabilities that can be exploited and some of the hackers and brokers that operate within governments and on the black market for computer exploits. We review some of the 21st-century milestones in the escalating advancement of offensive cyberwar capabilities and the lagging efforts toward cyber-defense. At the end of the post, we will offer a few thoughts on how the world might be able to move forward before major world cyberwar breaks out.
II. Vulnerabilities
The purpose of a cyber attack is to gain unauthorized access to the computer, smart phone or network of another individual or organization, in order to spy, steal, ransom, disrupt or damage stored information or hardware devices. Some of the most common types of cyber vulnerabilities are summarized in Fig. II.1. Malware is the generic name given to malicious software installed within a target system to accomplish the invader’s goals.
While access to a target system can sometimes be gained by guessing or trial-and-error searching for passwords (an approach effectively blocked by now widely used two-factor authentication protocols), most malware attacks rely on some action taken by the target system’s owner or user. This might consist of inserting a thumb drive that has been contaminated with malware. But the most common approaches utilize phishing scams, where a user is enticed to click on a malicious link or open an infected file attached to an e-mail designed to appear as though it comes from a reliable source. Spear phishing refers to more targeted phishing attacks that focus on specific types of individuals, such as system administrators or device control engineers.
In man-in-the-middle attacks, hackers insert themselves between two users or systems in communication, to steal data in a cyber update of more traditional eavesdropping techniques in historical spy repertoires. For example, in recent years Russian government cyber teams have penetrated the U.S. electrical grid system in part by stealing information gained through a redirection of grid operators’ web traffic through the intermediary of Russian hackers’ machines. Such redirection is often accomplished via DNS attacks, in which malevolent actors exploit vulnerabilities in the Domain Name System (DNS) to divert visitors intending to reach a desired web page destination to a malicious site.
Denial of service attacks rely on inundating networks or servers with much more massive, spurious traffic than the systems are designed to bear, and thereby disrupting the ability to process legitimate requests. In SQL injection, cyber criminals upload malicious scripts in Structured Query Language (SQL), in order to view, modify or delete information stored in targeted databases.
But the true coin of the realm in the most destructive cybercrime and cyberwar attacks is the zero-day exploit. As illustrated in Fig. II.2, this relies on finding and exploiting vulnerabilities in commercial or open-source software, which allow the insertion of malicious sections of code, before the vulnerabilities are discovered or patched by the software developers. The term “zero-day” refers to the number of days the software vendor has had to patch the vulnerability at the time of the exploit.
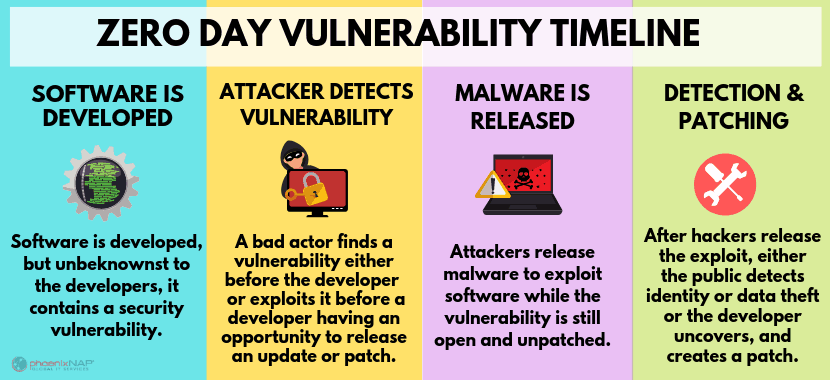
A zero-day exploit can infect computer networks without requiring any conscious activation by users responding to phishing scams. It can provide “backdoor” entry into computers or smart phones that facilitates access to data before it is encrypted for transmission and made difficult to decipher. This makes the discovery of zero-day vulnerabilities in widely used commercial or open-source software a prize goal of hackers, criminals, governments and software developers. It has led to a thriving black market in the buying and selling of these discoveries and of the exploits based on them, as we will explore in more detail in the next section.
One widely publicized example of the financial value of zero-day exploits is associated with the aftermath of the Islamic terrorist attack that killed 14 people and wounded 22 others at an office holiday party in San Bernardino, California in 2015. After the two perpetrators were killed in a shootout, the FBI recovered the work iPhone of one of them, Syed Rizwan Farook. However, their attempts to search Farook’s iPhone for evidence of connections to ISIS or other terrorist groups were frustrated by the new security measures Apple had incorporated the previous year in the iPhone 6 model.
Those measures were in large part a response to the worldwide security concerns that had been raised by Edward Snowden’s 2013 release of classified NSA documents revealing the U.S. government’s own use of zero-day exploits to spy on smart phone users, including even the leaders of some U.S. allies. (The Snowden release will be described in more detail in Part II of this post.) Apple had decided to automatically encrypt all data stored on their new iPhones, using an encryption key accessible only to those with password access to the phone, and not even to Apple itself. Furthermore, the phone’s hard drive would be automatically wiped if someone attempting access entered incorrect passwords ten times in a row.
Apple CEO Tim Cook refused to surrender the company’s reputation for protecting users’ privacy by yielding to Department of Justice pressure for the company to help the government unlock Farook’s phone. The Justice Department took Apple to court over the issue, but then suddenly dropped the case when they managed to find a hacker (unidentified to this day) with a zero-day exploit to break into Farook’s iPhone and bypass the Apple encryption. The exploit was not supplied to the FBI out of a sense of patriotism, but was rather purchased by the FBI for $1.3 million. That incident provides some sense of the scale of black market costs for a single zero-day exploit in hard-to-crack commercial software.
UPDATE: On April 14, 2021 a Washington Post article revealed for the first time that the 2016 backdoor entry into Farook’s iPhone had been carried out for the FBI by a small Australian “white hat” (i.e., “good-guy”) hacking company called Azimuth Security. The iPhone security features were bypassed using a chain of zero-day exploits developed by two Azimuth staffers: the company’s founder Mark Dowd, designated by a peer as “the Mozart of exploit design,” and researcher David Wang, who had previously won awards for innovative iPhone exploit development. They gained initial entry to iPhones using a vulnerability Dowd had discovered in open-source software from Mozilla that Apple adopted to permit accessories to be plugged into the iPhone’s lightning port. With the aid of two additional exploits, they were then able to gain control over the phone’s core processor and to bypass the password security feature. This sequence then allowed them to use brute force methods to cycle through potential passwords until they found the one that worked.
In the most sophisticated cyber intrusions to date, zero-day vulnerabilities found by hackers have been exploited over lengthy periods before the vulnerability has even been discovered, let alone patched, facilitating advanced persistent threats in which implanted malware goes undetected for a long time. The most recent example is the SolarWinds attack, in which Russian hackers managed to insert some 4000 lines of malicious code into a routine update of widely used network management software provided by the company SolarWinds, before that update was released to and adopted by many thousands of customers. This exploit gave the Russians a secret backdoor entry into some 18,000 networks, including those used at many Fortune 500 corporations and within the U.S. Departments of State, Treasury, Justice, Energy and Commerce. The exploit outsmarted the U.S. government’s Einstein cybersecurity software, on whose development the Department of Homeland Security had spent billions of dollars.
The SolarWinds hack was discovered accidentally by the cybersecurity company FireEye at the end of 2020, some eight months after the Russians initially burrowed into a wide array of U.S. government computers. Until now, the exploit appears to have been used mainly for espionage, but it remains an open question whether the Russians are simply waiting for the appropriate moment to use it to disrupt supply chains, manipulate data, or even destroy computers. Once an enemy is deeply embedded within government networks, it is a highly non-trivial task to eliminate their access.
UPDATE: On April 16, 2021 U.S. President Joe Biden announced a series of new sanctions against Russia in retaliation for the SolarWinds attack and for Russian attempts to interfere with the 2020 U.S. Presidential election. The sanctions include the expulsion of ten Russian diplomatic officials, as well as a number of moves to impose financial pain on both Russian oligarchs and Russia’s broader economy, for example by barring U.S. financial institutions from buying Russian government bonds,
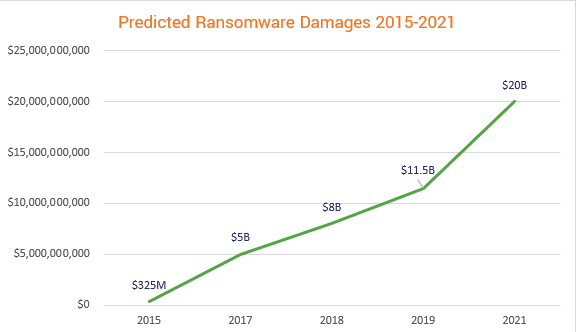
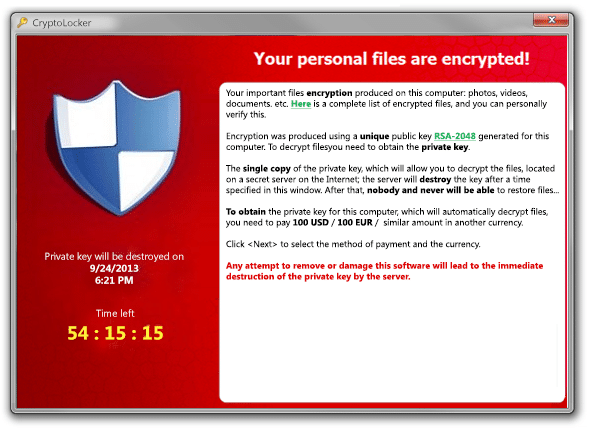
A rapidly growing cybercrime trend over the past several years (see Fig. II.3) is so-called ransomware, inserted into computers and networks either via successful phishing scams or zero-day exploits. In ransomware attacks a criminal or a nation-state (North Korea has used this approach extensively) gains unauthorized access to lock or encrypt the victim’s data, or to threaten its public release, unless a ransom is paid, often in Bitcoin or other cryptocurrency so that it is difficult to trace. An example of a ransomware attack is shown in Fig. II.4. Cybersecurity Ventures predicts that ransomware attacks on businesses will occur every 11 seconds throughout 2021, incurring global costs of about $20 billion, as one part of a cybercrime enterprise that will inflict some $6 trillion of damage. Particularly impactful ransomware attacks during 2020 have taken advantage of the worldwide COVID-19 pandemic to take down networks at hospitals and the company that supplies software used in vaccine clinical trials.
While cybercrime is a growing problem, the most dangerous cyber threats are posed by nation-states, which have the resources to find, purchase or steal extensive suites of zero-day vulnerabilities, and to assemble large teams of advanced hackers to turn those vulnerabilities into sophisticated exploits. The most sophisticated attacks often feature chains of zero-day exploits and deadly payloads a nation-state can stealthily insert into networks of adversary nations or targets of industrial espionage, or use to spy on their own citizens’ whereabouts, banking transactions and interactions with other citizens, domestic or foreign. Lockheed Martin has described the generic phases of such targeted attacks as a “cyber kill chain,” illustrated in Fig. II.5.
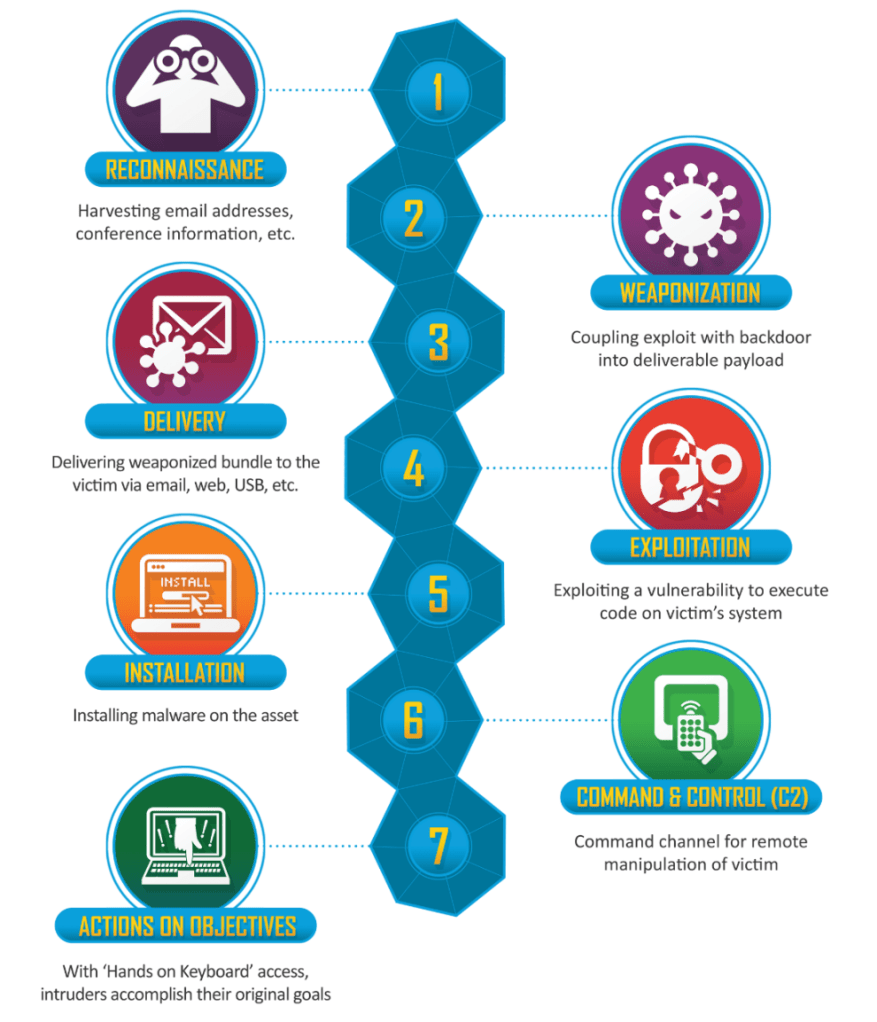
The command and control phase of the cyber kill chain allows a nation-state’s team to remotely operate the victim’s systems. For example, they can manipulate stored databases, altering voter registration rolls to disrupt democratic elections and sow political chaos. They can alter banking or stock exchange transactions to steal assets or cause financial meltdowns. They can deactivate the electrical grid or selected power plants in parts of an adversary nation. They can alter the mix of chemicals in purification plants to poison a community’s drinking water. They can change the firmware in Programmable Logic Controllers (PLCs) accessed by the victim’s computers, to destroy equipment whose operations are governed by those PLCs. They can alter the operation of dams to flood communities. These are not fanciful acts: all of them have already been accomplished or at least attempted during the 21st century! Some examples will be described in detail in Parts II and III of this post.
And in the most sophisticated attacks, the malicious implantation of the cyber kill chain remains hidden until the weapon of mass destruction is unleashed, and sometimes even for a long period of time afterward. In the classic example, to be described in detail in Part II of this post, the NSA, in collaboration with the Israeli Mossad intelligence service, launched in 2008 the first sophisticated cyberweapon – the so-called Stuxnet worm – to destroy many of the uranium-enriching centrifuges used by Iran on their path to develop nuclear weapons. But the attack was so clever and stealthy that more than a year passed before the worm moved beyond Iran, and the Iranians and the rest of the world understood that the gradual breakdown of centrifuges was not the result of faulty or aging hardware, but rather of a targeted cyberweapon from an adversary nation-state.
In the decade since the unveiling of Stuxnet, the development of offensive cyberweapons has escalated and spread worldwide, boosted in particular by the public release, starting in 2016, of exploit code stockpiled at the NSA and hacked or leaked by a group referring to themselves as the Shadow Brokers. Efforts toward improved cyber defense have picked up, especially since the Shadow Brokers’ releases, but still lag considerably behind offensive capabilities. We will cover milestones in the development of both offensive and defensive cyberwar capabilities in later sections of this post.
III. hackers and brokers
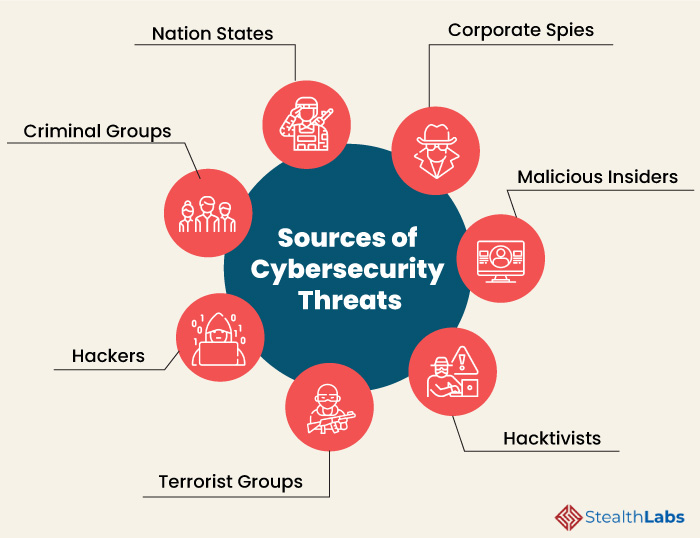
Figure III.1 summarizes the various classes of people who exploit software vulnerabilities. At the turn of the 21st century, as the number of worldwide users of personal computers, work stations and early internet browsers was skyrocketing, the search for vulnerabilities in widely used software products was carried out mostly by individual, anonymous hackers around the world. These folks spent many hours at their own computers uncovering bugs, occasionally for petty crime like stealing credit card information, but mostly for fun and a sense of pride at revealing the sloppiness of so-called professional software engineers. The hackers were not organized, but frequently shared their finds with other hackers by posting them on electronic mailing lists such as BugTraq or revealing them at the annual Def Con or Black Hat hacking conferences. They did not garner appreciation from the software development giants – Microsoft, Hewlett-Packard, Oracle, Sun Microsystems, later Google, Apple and Facebook – by revealing the vulnerabilities in their products. Instead, these companies often threatened the hackers with lawsuits or criminal prosecution, providing them with incentives to exploit the vulnerabilities they uncovered for their own profit.
It did not take long, however, before venturesome capitalists saw burgeoning market opportunities. John Watters bought out a failing cybersecurity company, iDefense, for $10 in 2002 and converted it to the first brokerage for computer hacks. iDefense began paying hackers nominal fees – at first only $75 per zero-day vulnerability – for exclusive access to their discoveries and then charging the software companies, and government agencies using the software products, annual subscription fees, to the tune of tens of thousands of dollars, for the information about their vulnerabilities so that they could patch their software before it was exploited by cyber criminals. And when companies balked that a reported bug was insignificant, an iDefense employee would demonstrate for them how the bug could be exploited to take control over their software or steal their customers’ data. Watters’ customers were often unhappy with the subscription fees and with what they considered iDefense’s immoral business plan, but as serious cyber attacks became more frequent, they continued to subscribe, even as the fee increased from year to year.
But soon enough, cyber criminals and government espionage agencies around the world began to see the enormous offensive benefit to obtaining exclusive access to serious zero-day exploits and keeping them hidden from the software vendors. The different players in Fig. III.1 had distinct goals, as summarized in Fig. III.2, but they often had common interests and exploit methods. So, they began to offer hackers bounties for exploits an order of magnitude higher than iDefense was paying them, sometimes reaching hundreds of thousands of dollars for a single exploit in hard-to-crack software. iDefense was rapidly getting priced out of the market it had helped to create, and Watters sold the company for $40 million three years after he had bought it for $10. And the open market for exploits that Watters had envisioned was replaced by a black market operated by underground brokers who paid high fees to hackers but demanded much higher fees from the government agencies or shady organizations willing to purchase rights to the exploits.
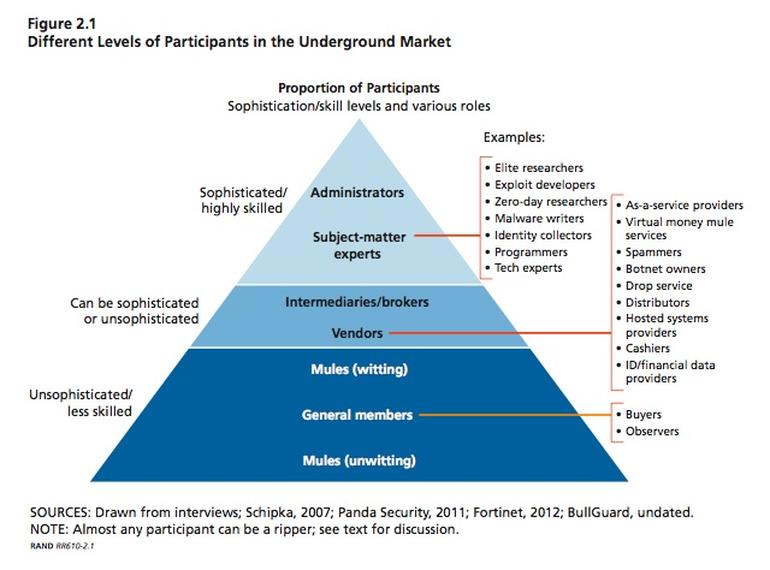
The black market has expanded steadily since its inception early this century and fueled rapid growth of cybercrime. Not only malware is bought and sold now, but also toolkits that help hackers steal login information, spear phishing services that trick users into opening viruses sent via e-mail, access to hijacked computer networks, and passwords and credit card data stolen in hacking attacks. A RAND Corporation study from 2014 has estimated that the cyber black market is potentially more profitable worldwide than the illegal drug trade. According to that study, the many players in that black market can be classified in a pyramid of technical sophistication shown in Fig. III.3, with the exploit developers at the top, the brokers intermediate, and most of the buyers, observers and unwitting carriers near the bottom. The general sophistication of computer users worldwide falls very low on such a pyramid, making vulnerability to cybercrime high. In Section V of this post, we will include some suggestions about how individuals and companies can try to protect themselves against cyber attacks, along with describing efforts at improved commercial cyber defense.
But one particular class of potential buyers for some zero-day exploits is quite tech-savvy, namely, the elite hacking groups that now occupy hidden places within intelligence agencies in many governments. These nation-state hackers work in stealth but develop and deploy the most sophisticated exploits known, in the service not of cybercrime, but of cyber espionage and cyberwar. In the U.S. the person most frequently credited with alerting intelligence agencies – first NSA, then CIA – to the enormous potential of zero-day exploits for espionage and destruction is James Gosler (see Fig. III.4). As a member of the Adversarial Analysis Group at Sandia National Laboratories in Albuquerque, New Mexico, in the mid-1980s, Gosler was charged with assuring the robustness of America’s nuclear arsenal to outside attacks. As part of the effort to analyze critical vulnerabilities in the microchips used to control nuclear weapons, he tried to demonstrate to his colleagues that an adversary could subvert allegedly secure computer code with malicious inserts that would be very difficult to detect. He succeeded even beyond his own expectations: the team of evaluators at Sandia was never able to find the malware he implanted as a test.

News of Gosler’s groundbreaking test exploit reached the NSA, which invited him to spend some time at their headquarters in Fort Meade, Maryland (see Fig. III.5) in 1987, to teach their analysts a thing or two about software vulnerabilities. None of the NSA team was able to detect Gosler’s malware, even though it was inserted into an application featuring only 3,000 lines of code. The experience opened their eyes to the wide array of possibilities for nearly undetectable subversion of commercial or open-source code that then featured sometimes hundreds of thousands lines of code, and today often reaches hundreds of millions lines of code. Gosler ended up spending two years as NSA’s first “visiting scientist,” helping the division now known as Information Assurance to “track down Soviet implants and anticipate those of every other adversary who sought to do the United States harm.”

The NSA recognized, however, that attaining foolproof cyber defensive capabilities was likely an unachievable goal. So, they sought to create their own elite hacking team and to stockpile secret zero-day vulnerabilities they could exploit as offensive cyberweapons against adversaries, for either surveillance, preemptive or retaliatory attacks. These offensive cyberweapon specialists are housed in an NSA division known until recently as Tailored Access Operations (TAO). After Gosler returned to Sandia in 1990, he continued to supplement his responsibilities for Sandia by aiding NSA’s classified development of zero-day exploits for cyber offense. The CIA soon became jealous of NSA’s rapidly expanding budgets and intelligence capabilities. And in 1996 CIA Director John Deutsch hired Gosler to direct the CIA’s new Clandestine Information Technology Office (CITO), charged with developing world-leading digital surveillance tools.
At the turn of the 21st century, the only other countries capable of comparable investment to the U.S. efforts in developing their own mission-critical zero-day exploits were Russia and China. The NSA was infected with hubris, adopting a philosophy that “nobody but us” (often abbreviated as NOBUS) had the ability to develop and deploy such sophisticated cyber weaponry. Developments during the past decade have exposed the naïveté of that philosophy. As an indication of how offensive cyber hacking capabilities have expanded in other countries since 2000, Microsoft engineers working on revealing the details of the extensive 2020 SolarWinds attack have estimated that well over 1,000 engineers must have been involved in the development and deployment of this attack, presumably from within Russia’s Foreign Intelligence Service. In the U.S., efforts at the NSA and CIA have by now been supplemented by a Cyber Command established in 2009 by the Obama administration at the Pentagon, to deploy offensive cyber attacks.
By the present day, a number of other countries – including North Korea, Iran and Israel – have built up considerable capabilities of their own to develop zero-day exploits. And many other countries, and even smaller organizations, can afford to purchase exploits on the cyber black market. The hackers who sell the vulnerabilities they uncover to brokers are spread across the globe. In some countries, hacking has developed into one of the most reliable ways of earning a living wage. Experienced hackers often train newer converts at regional or international Black Hat hacking conferences. The prices paid by brokers for zero-day exploits have continued to escalate.
One of the few cyber vulnerability brokerage firms to advertise publicly and take their business at least half above ground is Zerodium, established by the French Algerian Chaouki Bekrar, who relocated his brokerage in 2015, after a European Union crackdown on cyberarms dealing, from Montpelier, France to Washington, D.C. The Zerodium website advertises its operations this way:
“ZERODIUM is the world’s leading exploit acquisition platform for premium zero-days and advanced cybersecurity capabilities. We pay BIG bounties to security researchers to acquire their original and previously unreported zero-day research. While the majority of existing bug bounty programs accept almost any kind of vulnerabilities and PoCs but pay very low rewards, at ZERODIUM we focus on high-risk vulnerabilities with fully functional exploits and we pay the highest rewards (up to $2,500,000 per submission).”
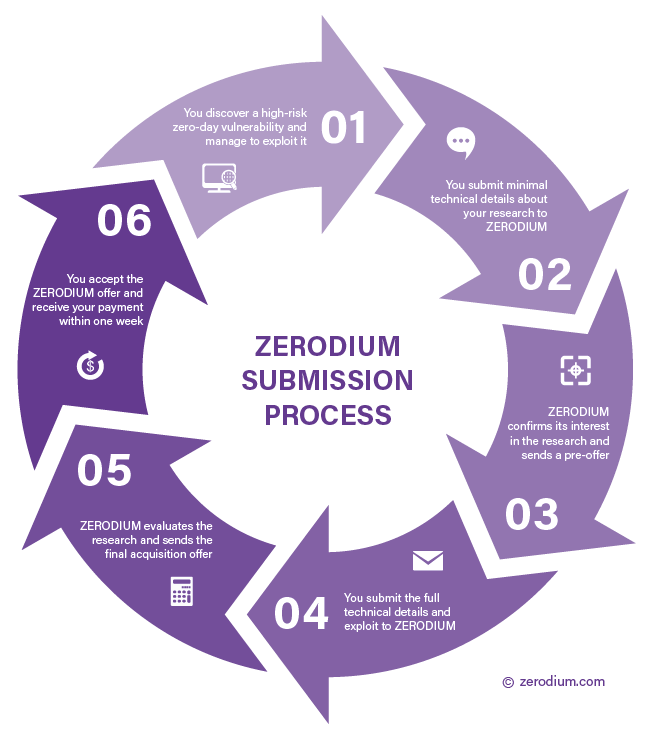
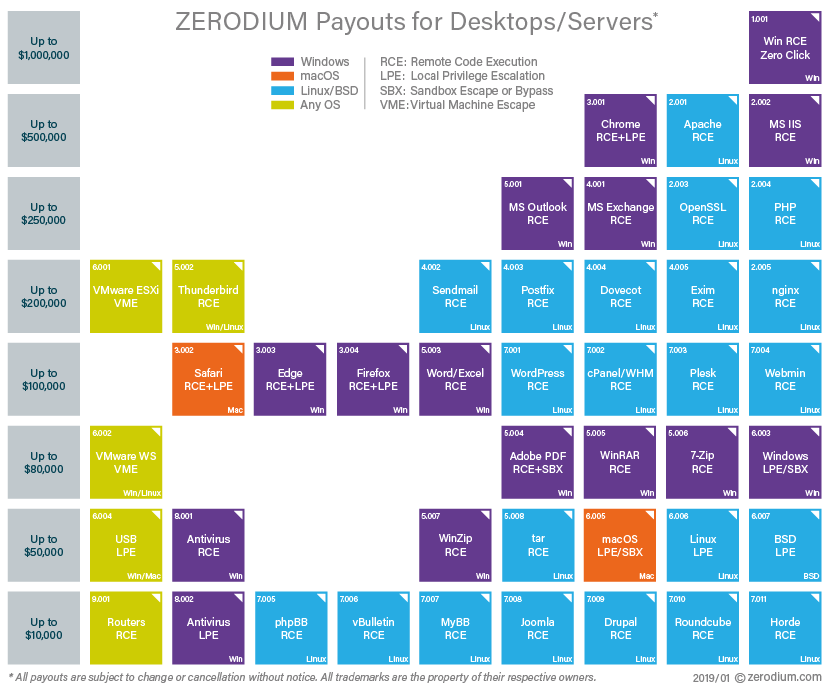
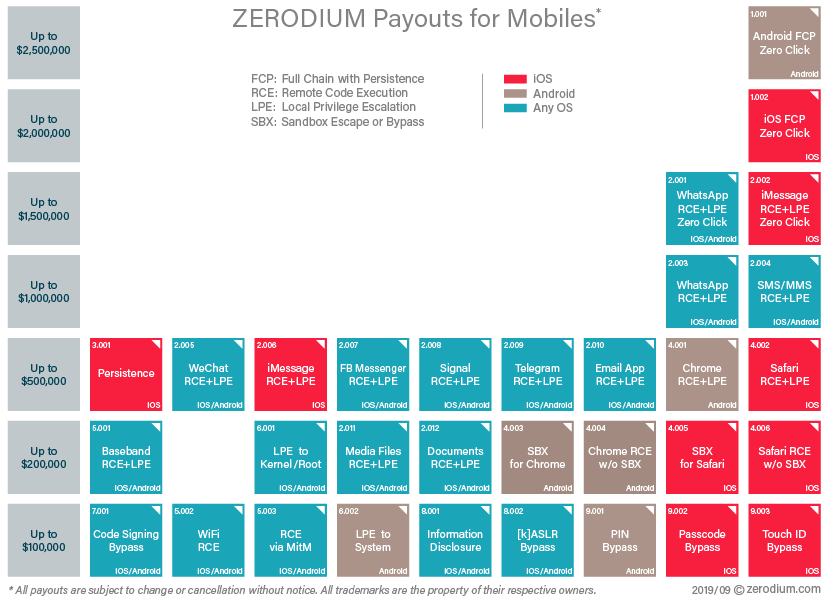
They describe the zero-day submission process via Fig. III.6, emphasizing that “Payments are made in one or multiple installments by bank transfer or cryptocurrencies (e.g. Bitcoin, Monero, Zcash).” And they advertise the specific bounties they will pay via the matrices shown in Figs. III.7 and III.8, reflecting their business model: “The amounts paid by ZERODIUM to researchers to acquire their original zero-day exploits depend on the popularity and security level of the affected software/system, as well as the quality of the submitted exploit (full or partial chain, supported versions/systems/ architectures, reliability, bypassed exploit mitigations, default vs. non-default components, process continuation, etc).” As is clear from Fig. III.8, the most highly valued exploits today are ones that facilitate break-ins to iPhones or Android phones without requiring the users to click on anything.
And to whom does Zerodium sell the exploits they acquire, presumably at (unadvertised) prices considerably higher than the bounties they pay hackers? Bekrar claims they sell only to NATO countries or “NATO partners,” but he retains a laissez-faire attitude concerning the ultimate uses to which the exploits are applied: “…if you sell weapons to someone, there’s no way to ensure that they won’t sell to another agency.” But he certainly does not support selling or, heaven forbid, donating the exploits to the software vendors so that they might patch the vulnerabilities: “We don’t work as hard as we do to help multi-billion dollar software companies make their code secure. If we wanted to volunteer, we’d help the homeless.”
Between the ability to purchase critical zero-day exploits from brokers such as Zerodium and worldwide access to NSA’s stockpile of exploits following the Shadow Brokers release, the world is now in a very dangerous place of vulnerability to cyberweapons. There is no opportunity for a non-proliferation treaty comparable to that established globally for nuclear weapons, because lots of dangerous cats are already out of the bag and many nation-states are invested in capturing their share of those cats. We review some of the major episodes in the advancement of cyberweapon attacks in Part II of this post. And we will comment in both Parts II and III on international efforts to craft some sort of digital “Geneva Convention” that would impose agreed-upon restrictions on at least the peacetime targets of cyberweapons.
