March 28, 2021
Updated April 22, 2021
IV: Milestones in Nation-State Cyber-Offense
In the early years of the 21st century, the U.S. National Security Agency (NSA) had amassed a number of tools for cyber surveillance. Following the 9/11 terrorist attacks, there was a massive effort to increase our knowledge of foreign terrorists, particularly non-state actors. With the passage of the Homeland Security Act in 2003, cyber-security officials had what seemed like a green light to investigate any groups that might pose a threat to the U.S. As the agency charged with monitoring, collecting and processing data related to intelligence and counterintelligence operations, the NSA was the group tasked with capturing and analyzing data. But, as summarized by Nicole Perlroth, “the NSA’s work was riddled with conflicts of interest and moral hazards.” Apparently, little time was spent wondering what would happen if other nations or groups got their hands on the methods exploited to break into supposedly secure computer systems and data repositories. Other useful books on cyber-warfare are Dark Territory by Fred Kaplan, and The Perfect Weapon and Confront and Conceal by David Sanger.
Furthermore, the companies whose products the NSA was hacking were often American companies with global reach, such as Microsoft, Facebook and Google. Perlroth again: “Nobody apparently stopped to ask whether in their zeal to poke a hole and implant themselves in the world’s digital systems, they were rendering America’s critical infrastructure … vulnerable to foreign attacks.’
Staff at the NSA seemed to believe that their only problem was to increase the secrecy surrounding their operations. In addition, American security officials at NSA and CIA had great confidence, as would alas turn out to be misplaced, that the U.S. was decades ahead of other major powers in the ability to discover and exploit loopholes in digital systems.
In this atmosphere, and with little or no public discussion of the risks involved, the U.S. created the rules for cyberwarfare. And they then put them into action. The U.S. determined that it was acceptable for a nation to launch an attack on another country’s digital infrastructure, in the absence of a declaration of war. In this Section, we will review a number of major episodes in cyber attacks by nation-states in the last 20 years.
Stuxnet: The Ultimate Trojan Horse
In June 2007, the U.S. was worried that Iran was making rapid progress in enriching uranium, a key step towards constructing nuclear weapons. As the state most threatened by an Iran with nuclear capabilities, Israel was putting considerable pressure on the U.S. to take action against Iran, or to allow the Israelis to conduct an attack on Iran’s facilities, particularly the Iranian site at Natanz. Figure IV.1 is a photo of the Iranian defense facility at Natanz.

Figure IV.1: A photo of the Iranian facility at Natanz. Here, the uranium isotope U-235 can be separated, and eventually used to construct a nuclear weapon.
At Natanz, the Iranians had built an enormous facility, with much of it underground, fortified under many layers of rock. That facility contained thousands of gas centrifuges, which were used to separate different isotopes of uranium. Figure IV.2 shows a schematic picture of a gas centrifuge that could be used to separate the fissionable isotope U-235, an isotope that occurs naturally in very small quantities, from the much more abundant U-238. A gas of uranium atoms is pumped into the chamber of a centrifuge. The centrifuge is then rotated at extraordinarily high speeds – up to 100,000 rotations per minute. In this process, the slightly more massive U-238 tends to collect near the bottom of the centrifuge, while the top contains more U-235. After the gas at the bottom is removed from the centrifuge, the remaining mixture at the top contains a slightly higher fraction of U-235 than the original.
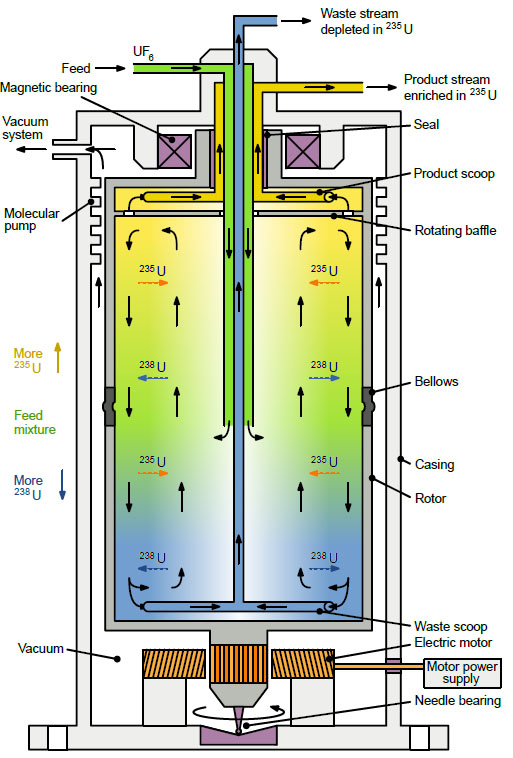
Figure IV.2: Schematic picture of a gas centrifuge. Uranium gas, with trace amounts of the isotope U-235, is piped into the centrifuge. Spinning the gas allows one to increase the fraction of U-235 in the remainder.
The slightly enriched gas is once more sent through a centrifuge. After repeating this process many times, eventually one can extract enough enriched uranium U-235 to construct a nuclear weapon.
The U.S. was opposed to participating in a pre-emptive military strike on the Natanz facility; they estimated that such an action would either start a war, or would result in Iran striking at Mideast oil fields, and/or attempting to close the Straits of Hormuz and block shipments of oil from the Mideast. An alternative was suggested: to utilize cyberweapons in order to interfere with Iran’s efforts to obtain nuclear capability.
According to Nicole Perlroth, the U.S. and Israel came up with a plan to attack the computers that monitored the gas centrifuges. The large centrifuges that are used to separate uranium isotopes are six feet tall. Because they spin at such high velocities, it is essential that the centrifuge speeds be carefully monitored, and that they be perfectly balanced. If the centrifuges spin too fast, the rotors can shatter, while if they slow down abruptly, the entire centrifuge could separate from its moorings.
The U.S. and Israel knew that the Iranians used Siemens centrifuges that were monitored by specialized computers called Programmable Logic Controllers (PLCs). The Natanz facility also used computers running Microsoft Windows software. Beginning in 2008, Americans from NSA and the CIA worked in collaboration with Israelis from Mossad, together with representatives from each of their national defense laboratories, on a program code-named Olympic Games.
The plan was exceptionally complicated, and its execution required the deployment of a number of top-secret zero-day exploits. Nicole Perlroth states that as many as seven zero-day exploits were used in the Olympic Games mission: four different zero-day exploits to gain access to the Microsoft Windows computers; and another three for the PLC computers that controlled the Natanz gas centrifuges. Because the Natanz facility was “air-gapped,” or separated from direct interaction with the Internet, the “worm” (or malicious program) had to be plugged into the computers that ran Microsoft Windows. This was accomplished by using a USB flash drive containing the malware code that would eventually be named ‘Stuxnet;’ apparently the name arose from an amalgamation of the names of two keywords found at the beginning of the computer software: ‘Stub’ and ‘mrxnet.’ The flash drive was either plugged directly into one of the Natanz computers by a spy; or the flash drives were left lying around the facility, and one was inadvertently plugged in by an employee.
A schematic diagram of the Stuxnet operation is shown in Fig. IV.3. Once the Stuxnet program is plugged into a Microsoft Windows computer, it infects all other Windows computers on the same network. It then assesses the system. For systems that employ the precise array of Siemens PLCs that were used at Natanz (for example, the Natanz PLCs each controlled a cluster of 164 centrifuges), the worm then compromises the PLC computers. The worm thus spread indiscriminately, but it was specially tailored to become operational only for computer systems arranged in clusters such as were present at Iran’s Natanz facility. In addition to the safeguards placed on the program, so that it would only become operational on systems that had the exact structure as the Natanz nuclear facility, the program contained instructions to erase itself on June 24, 2012.

Figure IV.3: A schematic diagram of how Stuxnet worked. The malware infects Microsoft Windows, and then spreads to PLCs. Eventually the worm takes control of the centrifuges.
Once inside the PLCs, for 27 days the Stuxnet code did nothing except observe the monitoring of the centrifuges. The code observed the speed of the centrifuges — the U.S. and Israel knew that the Iranians employed centrifuge speeds between 800 and 1100 revolutions per second (Hertz). If the centrifuges were running at the correct speed, the code hijacked the Step 7 Siemens PLC controls; this was the software that controlled operation of the gas centrifuges. Stuxnet gave instructions that increased the centrifuge speed to 1400 Hertz for 15 minutes. The code then remained dormant for another 27 days, at which time the code caused the centrifuges to run at 2 Hertz for 50 minutes. The code once again went dormant for 27 days, and then repeated the cycle multiple times.
The periodic rapid increase and rapid decrease in rotation speed would be likely to initiate one of three outcomes: it could cause the rotors to break; cause the entire centrifuge to fly off its base; or stop the centrifuges. Yet another part of the code sent pre-recorded false data back to the operators, that indicated the centrifuges were working fine.
The entire operation was, at the time, the largest and most elaborate cyber-attack yet known. Apparently the operation required the efforts of teams of NSA cyber-experts and code-writers, engineers and nuclear physicists with knowledge of isotope separation techniques, CIA spies and experts on Iranian defense systems. These groups were complemented by their colleagues in Israel; in particular, the Israelis had built a replica of the Natanz site at their own nuclear test facility in Dimona, so they could ‘field-test’ the Stuxnet code.
At first, Stuxnet appeared to be a stunning success. Deployed in late 2008, by 2010 intelligence operatives reported that some 2,000 of Iran’s 8,700 centrifuges had been destroyed. Satellite photos showed Iranians carrying loads of centrifuges away from the Natanz site. Nuclear inspectors from the International Atomic Energy Agency also observed Iranians discarding large numbers of centrifuges. Apparently the Iranians suspected that the isotope-separation program was being sabotaged. Suspicions were raised, and workers began to be accused of causing the problems. A few Iranian physicists and engineers active in their nuclear program were murdered: it is not known whether they were killed by the Iranians or assassinated by the Israelis.
At first sight, this cyber-attack appeared to have accomplished all of its objectives. Approximately 25% of the Iranian centrifuges were destroyed, and the Iranians seemed unaware of the source of their problem. The Stuxnet operation had dramatically slowed Iran’s progress towards building its own nuclear weapons. And no shots had been fired, no troops deployed, and no cut-off of Mideast oil to the West. At this point, the Americans were confident that Stuxnet had been an unqualified success. It seemed to have worked exactly as planned, which validated American confidence that branches such as NSA were unparalleled in the world. Our access to “zero-day” exploits was unmatched, and it appeared that our ability to mount such a massive operation (the Stuxnet code was half a megabyte in size, and it was also written in multiple computer languages, including C and C++) was unmatched. What could go wrong here?
UPDATE: (Apr. 20, 2021) On April 10, a large explosion took place at Iran’s Natanz nuclear facility. At present, the extent of the damage is uncertain; on previous occasions, Iranian officials have downplayed the severity of a setback, while acknowledging much more serious damage at a later date. The explosion occurred in the underground area that houses the thousands of centrifuges that are used to enrich the isotope U-235 that occurs in naturally occurring uranium. Iran officials initially confirmed that the explosion took out all of the power in the underground facility, and that it also destroyed the backup power supply. A couple of days later an Iranian Parliament spokesperson, Alireza Zakani, said that “several thousand centrifuges [were] damaged and destroyed.” At the moment, no other reports have confirmed Zakani’s statement. It is believed that the damaged centrifuges were part of the first generation of IR-1 centrifuges.
It appears that the explosion could set back Iran’s nuclear program by up to several months. Iran accused Israel of the attack, and vowed that they would retaliate. In addition, Iran said that it would subsequently enrich uranium to 60%, which would constitute a major escalation of their nuclear program (previously, Iran was enriching uranium to the 20% level).
Most experts agree that the April 10 explosion was not the result of a cyberattack. The New York Times quoted an unnamed official who said that the explosion was caused by a bomb that had been smuggled into the Natanz plant and then detonated remotely.
Generally, Israel does not officially acknowledge its participation in strikes against nuclear programs in Middle Eastern countries. But both American and Israeli officials privately agreed that Israel was behind the latest incident at Natanz. There could be three reasons behind the Israeli attack on the Natanz facility. For some time, Israel has taken steps to prevent Middle Eastern nations from developing nuclear weapons. On two previous occasions, they bombed Mideastern countries in order to prevent them from developing nuclear weapons. Another possibility is that Israel struck at the Natanz facility in an attempt to derail the multi-national talks attempting to re-start the agreement with Iran on halting their nuclear weapons program. Talks between the U.S., Iran and the other signatories of the Joint Comprehensive Plan of Action (the multi-national agreement that was brokered during the Obama Administration, but was abandoned by President Trump) began just one week earlier in Vienna.
Another possibility is that the Israeli attack on Natanz was intended to impact Israel’s domestic politics. At this time, a fourth Israeli election in the last two years has not produced a clear-cut winner. Benjamin Netanyahu’s Likud party is attempting to forge a coalition with other groups; it is conceivable that this latest attack could increase Netanyahu’s standing with other parties that might form a coalition with Likud.
Stuxnet Unchained:
In the first quarter of 2010, it appeared that the American confidence in NOBUS (“nobody but us has this capability”) was well founded. However in June, 2010, everything changed. It was realized that the “worm” had escaped the Natanz facility. Two theories, both unproved, have emerged to explain why Stuxnet became released outside of Natanz. The first hypothesis is that the Israelis felt that Stuxnet had not been sufficiently damaging to Iran’s centrifuges, so they released another version of the malware, and it escaped that facility. A second hypothesis is that an Iranian working at Natanz plugged his own laptop into the nuclear facility’s computers, and it infected his own internet-connected computer and subsequently spread.
In any case, by summer 2010 Stuxnet had spread to computers in many other countries. Countries with infected computers primarily included Iran, Indonesia and India, which collectively accounted for 85% of the compromised computers. The Stuxnet code was studied by experts at many computer laboratories, including the Kaspersky group in Russia, Microsoft, Symantec, and German computer researcher Ralph Langner. The conclusion reached by the Kaspersky group, and reinforced by subsequent reporting on the attack, was that the worm was so complicated it could only have been constructed “with nation-state support.” However, it appeared to be a highly sophisticated worm that had no detectable consequences. Langner was the researcher who deciphered its intent. The code’s search for Siemens controllers and the repeated appearance of the number 164 led him to discover that it had been precisely targeted at the Natanz facility centrifuges.
Since it was aimed at Iran, it was assumed that the Israelis and the U.S. were responsible for it. But at the end of his TED talk on cracking Stuxnet, Langner answered a question about its origins by saying: “The leading force behind that is the cyber superpower. There is only one, and that is the United States… fortunately, fortunately. Because otherwise our problems would be even bigger.” Investigative reporting has subsequently established that this was correct. But the problems were about to become even bigger. Here is video of Langner’s TED talk.
Once the Stuxnet code was dispersed worldwide, many groups could access and analyze it; this led to a number of developments, all of them ominous.
- Computer manufacturers and computer security firms were alarmed that the NSA had identified a number of vulnerabilities in software and hardware. Instead of alerting the companies so they could release “patches” that would close the loopholes, NSA instead hoarded the exploits, and used them for their own purposes.
- Countries became aware that the U.S. was willing to utilize its knowledge of cybersecurity to initiate an attack on another country’s (Iran) infrastructure. First, this made other countries aware of the possibilities of cyber warfare; second, by examining the structure of Stuxnet, they could use similar methods to attack and penetrate computer systems in other countries or in industry.
- The same exploits that the U.S. embedded in Stuxnet could be returned, not only by nation-states, but also by small groups of hackers. At risk now were “businesses, hospitals, electric utilities, nuclear plants, oil and gas pipelines, [and] transportation systems,” all of which were monitored by computer systems analogous to the Siemens PLCs that were hacked by Stuxnet.
- To make matters worse, it was now becoming more difficult to ensure that cyberweapons would remain in the hands of the “white hats.” This was especially true for lone-wolf hackers, or for companies that developed cyberweapons on contract. One such company, Vulnerability Research Labs (VRL) was discussed in Nicole Perlroth’s book. They specialized in finding zero-day exploits and developing them so that they could be used as cyberweapons. Perlroth asked one VRL employee what precautions they took when working with foreign hackers, to ensure that the exploits they developed were being used for allies and not enemies. “’We didn’t care,’ he said. ’We just did whatever it took to produce the goods.’”
Edward Snowden:
Edward Snowden is an American cyber-security expert who worked for several government agencies and government contractors. In 2006 he was hired by the CIA where he worked in their global communications division. After his proficiency in computing was acknowledged, he received CIA training in computer technology and was then stationed in Geneva, Switzerland as a computer security specialist.

Figure IV.4: Computer security specialist Edward Snowden.
Snowden left the CIA in 2009 and was then hired by Dell, where he was assigned to an NSA office in Tokyo. There he was responsible for advising the NSA on maintaining security against attacks by hackers, particularly from China. Snowden reports that during this time, his work shifted to “cyber counterintelligence.” He asserts that he was a high-level cyber officer with Dell, and that part of his job entailed consulting with the CIA’s top information officer and with the chief technology officer of the CIA.
By April 2012, Snowden had become disenchanted with the spying operations of the NSA. He claims that he made numerous attempts to share with superiors his concerns about the legality and morality of the NSA’s spying on both foreign and domestic citizens. Around this time, Snowden apparently began copying large numbers of files and documents that showed the operations of the NSA.
In March 2013, Snowden resigned from Dell and went to work for Booz Allen Hamilton, a company that had several defense contracts. Snowden had previously been working in Hawaii with the NSA, where he focused on electronic surveillance of China and North Korea. He continued this work in Hawaii for the two months that he was employed by Booz Allen Hamilton. He reports that his main efforts were focused on efforts to penetrate Internet and cell phone data traffic around the world. Snowden continued to copy top-secret NSA files; then he copied even more files.
In mid-May, 2013, Snowden told his superiors at Booz Allen Hamilton that he needed to travel from Hawaii to the States to deal with his epilepsy. However, instead of leaving for the U.S. mainland, Snowden flew to Hong Kong. On May 20, Snowden arrived there to meet Glenn Greenwald, who at the time was a correspondent for The Guardian. Snowden’s initial contact with Greenwald had been in Dec. 2012; at that time Snowden (using the alias Cincinnatus) indicated that he had sensitive documents he was willing to share with Greenwald. However, Greenwald balked at some of Snowden’s conditions for sharing information (one of those conditions was that Greenwald encrypt all his e-mail).
Snowden then contacted documentary filmmaker Laura Poitras, as Ms. Poitras had made a film about an earlier NSA whistleblower, William Binney. Around April 2013 Snowden began to send files to Greenwald and Poitras. The first published report about Edward Snowden and his revelations regarding NSA operations was a June 5, 2013 article by Glenn Greenwald in The Guardian. The story was then taken up and reported widely, including the Washington Post and New York Times in the U.S., and also papers in Germany, France, Sweden, Spain, the Netherlands and Australia. In June 2014, for their reporting on the NSA/Snowden story, Glenn Greenwald, Laura Poitras, Barton Gellman of the Washington Post, and Ewen MacAskill of The Guardian were awarded the 2013 George Polk Award. “The NSA reporting by these journalists also earned The Guardian and The Washington Post the 2014 Pulitzer Prize for Public Service for exposing the ’widespread surveillance’ and for helping to spark a ’huge public debate about the extent of the government’s spying.’”
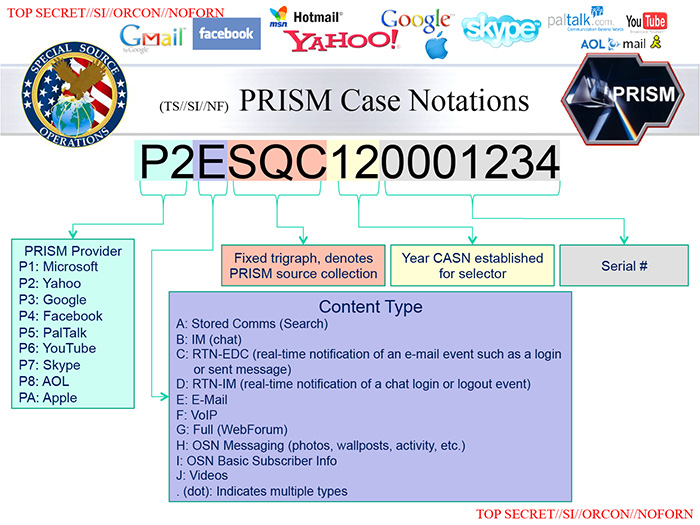
Figure IV.5: A slide explaining the operation of the top-secret NSA program PRISM, that allowed the NSA (with a court order) to spy on the Google and Yahoo accounts of Americans.
So what did Edward Snowden’s files reveal about the top-secret programs of the NSA and similar operations run by our allies?
- The program PRISM, that allowed for the court-ordered scrutiny of Google and Yahoo accounts of Americans. A slide from the information released by Edward Snowden is shown in Fig. IV.5.
- An NSA call-base that used a secret court order to require Verizon to provide them with daily call records of millions of Americans.
- An analytical tool called XKeyscore; it allowed the NSA to collect “almost anything done on the Internet.”
- The NSA had a surveillance program called MUSCULAR; with this tool it tapped undersea cables and was able to access the Google and Yahoo accounts of hundreds of millions of users worldwide. A hand-written slide showing how MUSCULAR worked is shown in Fig. IV.6.
- The NSA also tracked the sexual activity of people considered “radicalizers;” the idea was to use this intimate information if necessary to discredit those people. NSA employees also used agency tools to track their own “love interests;” they named this effort LOVEINT.
- Snowden’s files revealed that, in addition to suspected terrorists and activities of our adversaries such as North Korea, the NSA also spied on our allies, including countries such as Britain, France, Mexico, Spain and Italy. The NSA also spied on individual leaders, most notably German Chancellor Angela Merkel.
- In addition to the data collection efforts listed above, Edward Snowden claimed that the NSA could also conduct industrial espionage, particularly against foreign companies who might be competing with U.S. firms. Snowden gave the German company Siemens as an example of a foreign firm the NSA would spy on.
Snowden also showed that the total U.S. budget in 2013 for “dark intelligence operations” was $52.5 billion. Figure IV.7, taken from the material released by Snowden, shows how this funding was broken down by agency as well as by task. How many documents did Snowden surreptitiously copy? This is not known. However, Australian officials estimated that roughly 15,000 of their files were included in Snowden’s released materials, and British officials believe that at least 58,000 of their files were copied by Snowden. Initially, American officials gave a rather low estimate of the number of files taken by Snowden; however, a more recent review by the U.S. House Permanent Select Committee on Intelligence estimated that Snowden likely took about 1.5 million files.

Figure IV.6: A hand-written page that outlines how the operation MUSCULAR retrieves communications by tapping into underseas cables.

Fig. IV.7: A slide released by Edward Snowden that lists the U.S. budget for “dark intelligence operations;” this is broken down by the different agencies involved and by the different tasks under these operations.
From Edward Snowden’s point of view, he performed an enormous public service by revealing to the American people, and to the world, both the capabilities of the National Security Agency and others to tap into supposedly secure information, and the extent of the surveillance carried out by the NSA. It was quite a shock to Americans to realize that the NSA, an agency that insisted it surveilled only foreign systems and domestic terrorists, was actually carrying out massive intelligence gathering on millions of American citizens. In addition, foreign allies of the U.S. were outraged to see that the NSA was not only carrying out surveillance of potential foreign threats to American interests, but that they were also spying on the governments of our allies. Foreign companies were concerned that the NSA might be conducting industrial espionage against their own confidential programs and products.
Edward Snowden considers himself a whistle-blower and believes that he performed a public service in allowing Americans to understand the power and scope of the clandestine collection of data, and the cyber-weaponry at the disposal of the NSA. But how is he viewed by U.S. officials? Initially, it was clear that U.S. intelligence officials considered Snowden a traitor. In June 2013 Snowden was charged with violating the Espionage Act of 1917 and theft of government property. Government officials claim that material released by Snowden caused “great danger” to U.S. intelligence efforts. For example, it is claimed that after studying the materials released by Snowden, Islamic terrorists changed the way that they interact; they are said to have increased the use of couriers and to have changed to encrypted communications to avoid detection.
In 2015, the London Sunday Times reported that Chinese and Russian intelligence agencies had received more than 1 million secret files from Snowden’s material; they stated that this had gravely harmed British intelligence-collecting activities and caused them to close down some foreign activities.
There is very little common ground between Snowden’s own characterization of his motives and methods, and that of American defense and intelligence officers. For example, U.S. officials characterized Snowden as a minor government official, whereas Snowden claimed that he would regularly consult with the CIA’s chief information officer and its chief technology officer. U.S. officials also deny that Snowden had made numerous efforts to contact his superiors with his concerns about the scope and morality of the NSA efforts. While Snowden’s supporters tend to characterize him as “heroic” or “patriotic,” his detractors see him as a “dissident” and a “traitor.” In Snowden’s defense, he was not attempting to make money from his disclosures, and he felt that the world in general, and Americans in particular, needed to understand the incredible reach of the NSA intelligence programs.
Snowden claims that the “tipping point” for him was when James Clapper, the Director of National Intelligence, denied in Congressional testimony on March 10, 2013 that U.S. intelligence agencies carried out wide-scale surveillance of Americans. In support of this claim, it is true that Snowden quit his job at Dell just three days after Clapper’s testimony. However, this date is already months after Snowden first contacted Glenn Greenwald and offered to provide him with information about NSA activities.
Snowden received some measure of justification for his actions when, on Sept. 2, 2020, a federal court ruled that the U.S. intelligence services’ mass surveillance program collecting data from Americans was illegal and quite probably unconstitutional.
Whether you consider Edward Snowden a heroic whistleblower or a traitor, it is clear that the information he released has led to a much more complete understanding of the extent of U.S. programs that spy on people and governments around the world, including widespread domestic surveillance of our own citizens.
China Attacks Google and American Industry:
In December 2009, staffers at Google noticed that their computers were under attack from an unknown source. Security staff at both Google’s U.S. headquarters in Mountain View, California and their Swiss office in Zurich noticed what appeared to be a sophisticated and multi-pronged attack on their servers. This was clearly a much more professional assault on their computer systems than the normal work of a small group of hackers. Google enlisted the services of the cybersecurity firm Mandiant to locate the source of the break-in, and to suggest ways that Google could scrub their system of “back doors” that might have been planted by the attackers.
Eventually, the Mandiant team focused on the fact that Google employees in Beijing had been exchanging messages with their colleagues around the world using a Microsoft chat service. And each of the employees with problematic computer hacks had previously clicked on a link attached to a message that read “Go kill yourself.” After exhaustive efforts to locate the source of the attacks, and to remove the hackers from their systems, Google and Mandiant eventually reached the conclusion that the attack came from China. The source of the attacks was a group working for the Chinese government that the NSA had previously identified and given the name Legion Yankee.
Apparently there were two different groups working with Legion Yankee. The first included elements of computer groups associated with the Second and Third Departments of the Chinese People’s Liberation Army (PLA). The second group were Chinese computer professionals from universities and internet companies. The student and corporate computer hackers were reputed to be much more skilled than the PLA soldiers. And Google eventually determined that the goal of the Chinese hackers was to steal or infiltrate Google’s source code. If the Chinese were able to access and manipulate Google’s source code, this could provide them with enormous leverage, both immediately and in the long term. They could subsequently invade applications that utilized the source code, or they could spy on people (e.g., those they viewed as Chinese dissidents) who used particular apps, such as Google Maps. Alternatively, if they chose they could mount attacks that would cripple Google’s programs, or use this access to initiate ransomware efforts.
It turns out to be incredibly difficult for these large firms to determine whether their source code has been hacked or modified. For example, the source code for all of the Google apps contains roughly two billion lines of computer code, while the source code for the Microsoft Windows operating system is estimated to run to fifty million lines of code. Discovering minute changes at random locations in such massive codes is considered almost impossible.
The attacks on Google were merely one part of a massive and concerted Chinese attack on American industry and national defense systems. For example, Chinese attacks on the U.S. defense industry focused on companies involved with “aerospace, missile, satellite and space technology,” and also on “nuclear propulsion and weaponry.” After Google had determined that they were under cyber-attack from the Chinese, they shared their knowledge with other companies. The NSA also alerted companies that China was likely mounting cyber-attacks on their firms, with the intent of stealing their source code or accessing confidential information on their products, patents, and current research.
Companies that are known to have been hacked by the Chinese include computer firms such as Adobe, Intel and Juniper Networks, and in addition corporations such as Northrop Grumman, Dow Chemical and Morgan Stanley. In fact, the Chinese attempts at infiltration were so extensive that in 2012 James Comey, then Director of the FBI, stated “There are two kinds of big companies in the United States. There are those who’ve been hacked by the Chinese, and those who don’t know they’ve been hacked by the Chinese.”
Google then decided on how to respond to the Chinese cyber-attacks. Their decision to enter the Chinese market in 2006 had been a wrenching one, particularly for a company whose founding motto was “Don’t be evil.” Google co-founders Sergey Brin and Larry Page argued to their staff that allowing Google to operate in China would provide the Chinese people with access to immense amounts of information. Despite the fact that Google was required to allow the Chinese to block access of their citizens to information about subjects such as Tienanmen Square, the Falun Gong group, and the Dalai Lama, Brin and Page believed that overall both their company and the Chinese people would benefit from Google’s presence.
However, over time the Chinese had greatly expanded their list of taboo subjects; in addition, Google was under pressure from Congress, as they were seen as collaborators with an American enemy. So the Chinese cyber-attack on Google was seen as brazen Chinese interference with their company. In January 2010, Google made a public announcement that they had been attacked by hackers associated with the Chinese government. Because of these attacks, they announced that they would no longer continue to censor results on Google.cn. The Google executives realized that this action would subject them to an enormous financial hit, cutting them off from the world’s largest market of Internet users. Google then moved all of their Chinese operations to Hong Kong.
But the Google hierarchy believed that it would not be possible for China to continue indefinitely to prevent their citizens from accessing information that, in their words, “damaged national security.” In late 2010, Google co-founder Sergey Brin told a New York Times reporter, “I think that in the long term, they are going to have to open.” At least in the short term, Brin has been completely wrong. At that time, China enforced a complete ban of Google. And under new president Xi Jinping, China has tightened its control of information and imposed even more restrictions on foreign companies doing business in China.
China Watches Its Own Citizens:
The Chinese state has initiated a number of programs that keep watch on its citizens and their activities. These efforts have intensified in recent years, as technology has allowed the implementation of many forms of surveillance. This has become a big business in China; it is estimated that in 2016, Chinese expenditures on domestic security exceeded the figures for national defense by 13%. In 2017 the total Chinese expenditure on domestic security was estimated at $197 billion, and they accounted for half of the world’s expenditures on security cameras. Figure IV.8 shows a security camera setup in Tienanmen Square.

Figure IV.8: A Chinese security camera set up in Tienanmen Square.
The first effort is via surveillance cameras. As of 2019, it was estimated that the Chinese had installed 770 million surveillance cameras across the mainland. This is by far the largest number of such cameras anywhere in the world. This began in 2005 with the formation of the computer system Skynet. In addition to an almost ubiquitous presence of surveillance cameras in public areas in China, cameras have also been stationed in areas such as “mosques in the Xinjiang region, temples in Tibet, and the homes of dissidents.” Recently, the Skynet system has been upgraded, incorporating facial recognition software, combined with artificial intelligence (AI) and data mining techniques. In recent years, the Chinese government has also instituted cellphone apps, which are used for the purposes of national security, but the apps also allow citizens to report any suspicious activity. The reporting of unusual behavior to authorities has been a staple of the Communist system in China ever since the time of Mao Tse Tung.
In 2019, Comparitech reported that the top three cities in the world for computer surveillance are in China (Chongqing, Shenzhen and Shanghai, respectively), as are eight of the top ten cities in the world. The government claims that the surveillance cameras have enabled authorities to solve a number of crimes; however, critics claim that “one of the most important purposes of such a smart surveillance system is to crack down on social unrest triggered by petitioners and dissidents.” The Chinese have been using the latest advances in computer technology to enhance these surveillance techniques. For example, in 2016 China introduced a law that required all Internet companies to store all personal data and network logs for a period of at least six months.
China has been a world leader in developing and utilizing facial recognition software and artificial intelligence information to assist them in surveillance of their citizens. In 2018, law enforcement officials were equipped with Smartglasses that contain facial recognition software. The Chinese claim that this technology has allowed them to identify and apprehend drug smugglers and fugitives; however, the same technology also allows the Chinese to keep tabs on millions of their own citizens. China has also introduced software that tracks the location and behavior of users of video games. Although the stated purpose is to battle addiction to such games, it also allows the authorities to track the location of the gamers. The latest generation of Chinese Resident Identity cards also tracks the location of its holders.

Figure IV.9: A schematic summary of how biometrics and artificial intelligence allow computers to identify faces in images.
The most popular messaging app in China is WeChat. Any message that is sent through WeChat is monitored by the company that operates the app, TenCent. All conversations on this app are stored for a period of six months. In addition, TenCent has recently admitted that it has the ability to recover deleted WeChat messages. There has even been speculation that WeChat users outside of China may be having their messages surveilled. One of the reasons that WeChat dominates Chinese messaging is that competing apps such as WhatsApp and Messenger have either been blocked by Chinese authorities, or have even been forced out of the Chinese market.
For a while, Chinese Internet users were able to shield their communications by using virtual private networks (VPNs), but the government has cracked down on this as well. Beginning in 2017, the Chinese forbade the use of VPNs that were not approved by state regulators. Remaining VPN networks are required to use the state’s networks, which ensures that authorities can monitor their use.
Occasionally, the strict government control and surveillance of its citizens has some benefits. For example, during the recent COVID pandemic, the Chinese were able to monitor the health of its citizens because the state also required that health information be stored on cellphones monitored by the government. They were also able to enforce quarantines because they could follow the location of everyone with a cellphone. But the rigid centralization of information and the restrictions on speech and movement can also be used to control the population. This has had significant ramifications for regions where the state is concerned about control of minority populations. This has been seen in areas such as Tibet and Xinjiang (home to the Uighur minority group), and seems to be occurring now in Hong Kong. For example, in Hong Kong since early 2021, it appears that nearly every Hong Kong pro-democracy activist is either currently in prison or has left the territory.
Anna Mitchell and Larry Diamond have pointed out that recent developments in big data, artificial intelligence and facial-recognition software have finally enabled the Chinese government to collect and store “records on each citizen’s political persuasions, comments, associations, and even consumer habits.” The Chinese government has developed a “personal credit score,” that keeps track of a citizen’s behavior, politics, and other attributes. Mitchell and Diamond claim that “What China is doing here [with the personal credit score] is selectively breeding its population to select against the trait of critical, independent thinking.” They argue that China’s use of technology for repressive purposes will probably migrate to authoritarian regimes around the globe. And they call for democracies to “monitor and denounce this sinister creep toward an Orwellian world.”
China expert Kai Strittmayer comments on the use of technology by the Chinese to increase their control over the behavior of their citizens. “We have been told for so many years and decades by these tech prophets that every kind of new technology would actually serve the cause of freedom and would undermine and subvert authoritarian rule. Well, the Chinese … think that actually these new technologies give them new instruments that will perfect their rule.”
UPDATE: (Apr. 20, 2021) In a recent article in the Washington Post, Mike Abramowitz and Nate Schenkkan of Freedom House review their recent publication Out of Sight, Not Out of Reach. That report details examples of “transnational repression,” or examples of harassment, repatriation or even murder of citizens by their own countries, even when they are in exile. Prominently mentioned in this article are examples of harassment of Uighurs and Tibetans by China, even for people who are in exile. Probably the most well-known example of such repressive behavior is the murder of journalist Jamal Khashoggi by Saudi Arabian officials in their consulate in Istanbul.
In particular, China has used the WeChat app to spy on its citizens abroad. Chinese who are abroad and want to interact with friends and relatives in China have no alternative but to use WeChat, as it is the only messaging service allowed in that country. This “allows China to limit speech and organizing through censorship, to make threats without fear of any constraint by non-Chinese social media platforms, and to collect and organize data on users for political purposes with impunity.” As one example of this repression, “the family of a Uighur in Canada is detained in a labor camp in China; when the family gets out, they phone and warn their exiled daughter to keep quiet, while a Chinese official looks on.”
Authoritarian governments now routinely refer to dissidents as “terrorists.” If democracies accept these designations without investigating them, they are liable to accept repressive measures by autocracies as being legitimate parts of the “war on terrorism.” Freedom House found that Muslims are uniquely vulnerable to these labels, because of the existence of Islamist terrorist organizations. In its report, Freedom House lists several measures that democratic societies should take in order to strengthen protection for exiles living in their countries. With respect to cyber-spying, they recommend that we should “shut down commercial spyware exports that facilitate repression.” Otherwise, we risk allowing authoritarian governments to repress their own citizens even when they should be safely living in exile in a democracy. If we are not diligent in opposing these tactics, a likely outcome is that repressive societies will assume that these are acceptable tactics to use against their own citizens in exile.
North Korea Goes On The Offensive:
In 2013, Sony Pictures shot a film The Interview, starring James Franco as reporter Dave Skylark and Seth Rogen as his boss Aaron Rapaport. The premise of the picture was that Skylark and Rapaport travel to China to interview North Korean leader Kim Jong-Un for their TV show. However, they are recruited by the CIA to assassinate Dear Leader Kim. After a series of supposedly hilarious plot twists, eventually the duo steal Kim’s North Korean tank in an attempt to escape. Kim then stalks the pair in a helicopter, intending to kill the journalists and then initiate a nuclear war with the U.S. However, Skylark shoots down Kim’s helicopter, killing the North Korean dictator and avoiding a nuclear holocaust. Eventually, Skylark and Rapaport return to the U.S., while North Korea becomes a democracy and foreswears nuclear weapons.

Figure IV.10: A Sony Pictures poster for the movie The Interview, starring James Franco and Seth Rogen.
Well, no one ever accused the North Koreans of having a sense of humor. When the North Koreans got wind of the premise of the Sony picture, they promised “stern and merciless” retaliation if the film was released; furthermore, they characterized the film showing Kim’s assassination as “a blatant act of terrorism and war.” Sony subsequently moved the proposed release date from October to December 2014.
However, on November 24, 2014 Sony Pictures was hacked by a group calling themselves the Guardians of Peace (GOP). Sony Pictures staff who tried to log into their computers instead saw a graphic with a skeleton and the words “#Hacked by #GOP.” The hackers apparently destroyed about 70% of Sony’s computers as it could not be determined whether the malware had been removed, and the attack wiped data from many of Sony’s servers. The GOP hackers also leaked the Social Security numbers of employees of Sony Pictures. Although the North Koreans denied that they were the source of the cyber attack, experts were convinced that the attack originated in North Korea. For example, the exploits used to break into Sony were the same ones the North Koreans had used to attack South Korean banks and news broadcasters in 2013. Also, some of the attacks could be traced back to North Korean sites. And while denying responsibility for the hack, the North Koreans deemed this a “righteous attack.”

Figure IV.11: The screen seen by Sony Pictures employees on Nov. 24, 2014, showing the words “Hacked by #GOP” (for Guardians of Peace).
The destruction of data and computers was devastating to Sony Pictures. However, the initial media coverage centered on revelations uncovered in a massive dump of e-mails and other confidential documents from Sony. For example, Sony Pictures chairwoman Amy Pascal had made several denigrating and potentially racist comments about President Barack Obama; in preparing for a meeting between herself and the President, Pascal had suggested plugging a number of Sony movies with Obama – but all of these were films about slavery. Also, Sony CEO Kazuo Hirai had pressured Pascal to “soften” the assassination scene in The Interview (Japan, being much closer to North Korea, feared retribution over the film). After these revelations, Pascal announced that she was resigning her position.
Several other embarrassing memos also appeared in the North Korean data dump. For example, Sony executives commented that Angelina Jolie was “a minimally talented spoiled brat.” Perhaps even more damaging for Sony was the release of the scripts for several upcoming film projects, including the script for the James Bond film Spectre.
The Obama White House felt that the major issue involved here was one of free speech. They argued that Sony should not have halted distribution of The Interview in theaters, and that it set a bad precedent for movie companies to cancel projects if they were threatened by other countries. But Sony countered that although they were willing to release the film, a number of the largest movie theater chains had already declined to show the film. Eventually a compromise was reached, where the film was released just before Christmas in a number of independent theaters. Because of the immense publicity generated by the hacking of Sony Pictures, The Interview was considered a financial success, even though the critics treated the film rather savagely. Also, the film release on DVD was a success, particularly in Asia.
President Obama announced that the U.S. would “Respond proportionally” to the North Korean hack, “in a place and time and manner of our choosing.” Three days after Obama’s statement, the country of North Korea lost its connections to the Internet for one day.
The Shadow Brokers:
The Shadow Brokers are, in fact, a shadowy organization of hackers. They first surfaced in August 2016 in tweets from the Twitter account @shadowbrokerss. Their releases were written in a crude form of English, presumably to suggest a Russian origin. The first tweet from the Shadow Brokers was released on August 13, 2016. It began: “!!!! Attention government sponsors of warfare and those who profit from it !!!! How much you pay for enemies cyber weapons … We follow Equation Group [the name given by the Kaspersky Group to the NSA Tailored Access Operations or TAO group] … We hack Equation Group. We find many Equation Group cyber weapons … We give you some Equation Group files free, you see.”
But the Shadow Brokers made it clear that they were not releasing the ‘best’ Equation Group files. Those they proposed to auction off to the highest bidder. The bidders were supposed to make offers in bitcoin, and the Shadow Brokers promised to release the code and the passwords to the highest bidder. In a second message, titled “Trick or Treat” (released on Oct. 31, 2016) the Shadow Brokers released the names of seven previously unknown exploit tools (called DEWDROP, INCISION, JACKLADDER, ORANGUTAN, PATCHICILLIN, RETICULUM, SIDETRACK and STOICSURGEON).

Figure IV.12: Part of the message “Trick or Treat,” released by the Shadow Brokers on Oct. 31, 2016.
The initial tweet from the Shadow Brokers was met with considerable skepticism that this group had actually broken into the TAO servers and hacked actual exploits that they were hoarding. However, Nicole Perlroth reports that one of her cybersecurity contacts referred to the released materials as “The keys to the kingdom.” And Matthew Hickey, co-founder of the cyber security firm Hacker House, called one of the Shadow Broker releases “This is quite possibly the most damaging thing I’ve seen in the last several years.”
So, who are the Shadow Brokers? No one is really sure. Much suspicion is directed toward the Russians. Not only are they major players in the cyber weapons game, but Edward Snowden has stated that “Circumstantial evidence and conventional wisdom suggests Russian responsibility” behind the Shadow Brokers. But why would a nation release or auction off these exploits, rather than keeping and using them?
A second possibility is that an insider who worked with the Tailored Access Operations group at NSA might have leaked the exploits. In summer 2016, a former NSA employee and contractor with Booz Allen Hamilton, Harold T. Martin III, was accused of stealing thousands of pages of highly classified data and terabytes of secret computer programs from his employers. Martin eventually pleaded guilty to “willful retention of national defense information” and is currently in federal prison. However, the federal government has not been able to prove that Martin ever accessed the stolen materials – his lawyers claimed that his hoarding stemmed from mental health issues. So, it is not at all clear that Martin had anything to do with the Shadow Brokers.
However, the exploits released by the Shadow Brokers have been involved in several subsequent major cyber attacks. After their initial tweets, the Shadow Brokers continued to release NSA code. In April, 2017, they leaked the EternalBlue exploit. It used a vulnerability in Microsoft’s implementation of the Server Message Block protocol. In unprotected Microsoft systems, specially composed computer code was able to penetrate the computer and then insert malware code on the target computer. The NSA had known about this exploit for over five years, but they had not bothered to inform Microsoft of this vulnerability. However, in March 2017 the NSA had reason to believe that EternalBlue had been stolen and might be leaked to the public; so, at that time they alerted Microsoft to this possibility.
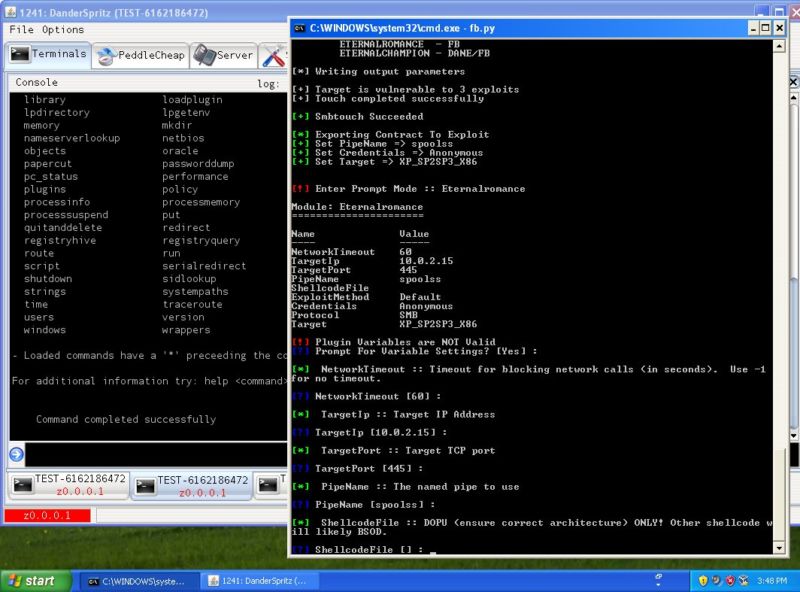
Figure IV.13: A portion of the exploit called EternalRomance. Like EternalBlue, it was released by the Shadow Brokers in April, 2017.
Microsoft quickly prepared a patch that removed this vulnerability; they issued a security notice and offered a patch for every computer system that they currently supported. But in May 2017, a cyber-attack called WannaCry used the EternalBlue vulnerability for a worldwide ransomware attack. Unfortunately, many Microsoft users had not installed the patches; also, users of currently unsupported Microsoft systems (Windows XP, Windows 8 and Windows Server 2003) were still vulnerable to the attack.
On May 12 2017, ransomware attacks using the EternalBlue exploit were launched across a number of countries around the world: this included “Russian railroads and banks, Germany’s railway, London hospitals, French automaker Renault, Indian airlines, four thousand universities in China, Spain’s largest telecom, Hitachi and Nissan in Japan, a hospital in Taiwan, movie theater chains in South Korea, nearly every gas station owned by PetroChina, and in the US, FedEx and small electric utilities.” Their data were encrypted, and they were told to pay a $300 ransom or their data would be permanently deleted.
The ransomware attack was dubbed “WannaCry,” a reference to an instruction “.wncry” in the attack code. The attack was quickly traced back to North Korea, as cybersecurity professionals were able to trace the attacking servers to those used in the 2014 North Korean attack on Sony Pictures. Furthermore, the North Koreans had rolled out the attacks before they had developed a way to deliver the decryption keys once the ransom was paid. Once people realized that their data was gone whether or not they paid the ransom, they stopped paying. Apparently North Korea netted only about $200,000 from the attack.
However, this was clear evidence that the exploits listed by the Shadow Brokers were powerful cyber weapons. The sloppiness of the North Korean attack, and the fact that Microsoft had issued patches to close the EternalBlue vulnerability, meant that the WannaCry attack was far less lethal than it might have been. It is notable, however, that at the time of the WannaCry attack the NSA was careful not to admit that one of its own exploits was a crucial element in this cyber attack.
The Russians Mess With Ukraine:
At the start of 2014, Viktor Yanukovych was President of the Ukraine. He was widely considered to be a puppet of Russian President Vladimir Putin. At that time, the Ukraine had brokered an agreement with the European Union that would have instituted economic and political ties between Ukraine and the EU. However, Yanukovych rejected that agreement, and instead accepted a loan bailout from Russia, and was pursuing closer ties between the Ukraine and Russia. This caused great consternation within the Ukraine; following a series of protests and demonstrations, Yanukovych left the Ukraine for exile in Russia.
For many years, Russian hackers have mounted cyber attacks on European countries; they have also used social media in attempts to sow distrust and chaos in democratic societies, with the aim of disrupting the solidarity between Europe and the U.S., and particularly in weakening the North Atlantic Treaty Organization. Ever since Yanukovych was deposed as President of Ukraine in favor of a more Western-oriented government, the Russians have repeatedly used that country as a “testing ground” for cyber attacks. Eventually it was determined that the attacks were originating from a Russian hacker group called Sandworm (that group is closely affiliated with other Russian hackers who are referred to as Fancy Bear).
Figure IV.14: The book Sandworm, by Andy Greenberg, recounts the work of Russian hacker group called Sandworm.
In 2014, in retaliation for the ouster of Yanukovych, the Russians had brazenly interfered with the subsequent election in the Ukraine. Social media in the Ukraine was bombarded with claims that Yanukovych was deposed in an illegal coup, or that he defected because of interference from Europe. Russian hackers “stole campaign e-mails, prowled for voter data, infiltrated Ukraine’s election authority, deleted files, and implanted malware in the country’s election reporting system that would have claimed victory for a far-right candidate.” At the last minute, election officials in the Ukraine discovered the Russian plot before the election results were reported to the media.
On December 23, 2015, Russian hackers attacked power stations in the Ukraine. They had embedded malware in Ukraine’s power grid that allowed them to seize control of the grid. The hackers then tripped the circuit breakers controlling the various power stations; at the same time, they shut down the emergency phone lines and also turned off the emergency power generators. This meant that the authorities in the Ukraine were forced to attempt to re-start their power stations using flashlights in the dark. The blackout lasted only six hours; however, it served as proof that the Russians were capable of crippling the Ukraine’s computers at any time. Furthermore, the attack also served as a warning to Europeans and Americans of the ability of Russia to utilize hacking exploits in devastating ways.
On June 27, 2017, the Russians carried out yet another cyber attack on the Ukraine. The attack affected computers and computer systems all over the Ukraine. Citizens “could not take money from ATMs, pay for gas at stations, send or receive mail, buy groceries, get paid, or monitor radiation levels at Chernobyl.” The attack also disabled the computers at the capital Kyiv’s two major airports and shut down the country’s shipping and logistics systems. Once again, the attack was traced back to Russia. This time Russia had used two of the exploits revealed by the Shadow Brokers: the EternalBlue exploit and a second exploit EternalRomance. And this attack also utilized a password-stealing exploit developed in France called MimiKatz. Eventually, authorities realized that the attack was triggered by malware that had been inserted into a computer program of a Ukraine firm that produced software used to calculate taxes, much like our TurboTax. When the company issued its annual software update, the malware infected every system that downloaded that code. The insertion of malware into a software update then automatically adopted by many thousands of users is the same basic technique behind the 2020 SolarWinds attack that was described briefly in Part I of this post, and which has also been attributed to Russian state hackers.
At first, authorities in the Ukraine believed that the cyber attack was a form of ransomware, and that they would immediately receive messages from the attackers, offering to repair the damage in return for a ransom. They assumed that the attack was analogous to an earlier ransomware attack called Petya. So, this new attack was named NotPetya. However, it soon became apparent that this was not a ransomware situation: the attack was simply designed to inflict the maximum damage to the Ukraine’s infrastructure and, once again, to demonstrate to Ukrainians just how much damage Russia and Vladimir Putin could inflict whenever they saw fit.
This 2017 attack occurred on the Ukrainian equivalent of our Fourth of July celebration. But, as earlier hackers had learned, the attack also spread widely outside of the Ukraine and around the world. Companies that did business with the Ukraine were likely to experience similar damage to their computer systems. Thus, companies such as the pharmaceutical giant Merck experienced shutdowns. International shipping companies such as FedEx and Maersk sustained major damage. Hospitals in various parts of the U.S., such as Virginia and Pennsylvania, could not access their computer systems. Even Russia was not spared the repercussions from their own attack, as computers at the Russian oil company Rosneft went down.
The extent of the damage caused by the NotPetya cyber attack is still not clear. Tom Bossert, who was once Donald Trump’s Dept. of Homeland Security advisor, estimated the worldwide damage at $10 billion; however, Nicole Perlroth states that many cybersecurity professionals consider this to be a dramatic underestimate of the true total. The NotPetya attack led some cybersecurity officials to suggest that the U.N. should consider a new Geneva Convention under which countries would agree not to attack civilian computer and control systems in times of peace. Microsoft president Brad Smith stated that “The world needs a new, digital Geneva Convention … We need an approach that governments will adopt that says they will not attack civilians in times of peace. They will not attack hospitals. They will not attack the electrical grid. They will not attack the political processes of other countries; that they will not use cyberweapons to steal the intellectual property of private companies. That they instead will work together to help each other and the private sector respond when there are cyberattacks.”
The U.S. initiated the round of nation-state cyber weaponry with their Stuxnet attack on Iran’s nuclear weapon development complex. At that time, the Americans were convinced that they were decades ahead of the rest of the world in this area. They thus had little interest in agreeing to a moratorium on such attacks. However, it is now clear that many countries have cyber weaponry tools that rival those of the U.S.: that list includes Russia, China, North Korea and Iran. And with the release of NSA exploits and computer code by the Shadow Brokers, these countries can now utilize American-made tools against us, or against other countries. An optimistic scenario is that now is the time for nations to agree to a set of binding rules against peacetime cyber attacks. The pessimist would suggest that we may have passed a tipping point: the current situation may be so dangerous and chaotic as to preclude international regulation of this situation. We will discuss efforts toward international agreements regarding cyber warfare further in Part III of this post.
