March 26, 2021
V. lagging efforts in cyber defense
Defense against cyber threats can take both proactive and reactive forms. The most obvious proactive measure is for software developers to focus on writing more secure code from the start. Software vendors can furthermore hire their own hacking teams to find vulnerabilities in the code they intend to market, or try to outbid brokers, government agencies and cybercriminals to purchase exploits in their own software directly from external hackers, so they can patch the vulnerabilities before they are exploited. They can provide software, hardware and training for users to reduce the frequency of unwitting exposures to cyber infections. Reactive approaches rely on cleaning up messes after cyber attacks are exposed. These include: updating software with patches to remove the exposed vulnerabilities; using anti-virus and anti-malware programs to limit the spread of reported cyber infections; and providing cybersecurity to detect infections within systems and networks, to neutralize their impacts, and to reconstruct information about the perpetrators. The reactive measures leave software vendors and users playing an eternal game of catchup by dealing with past crises while new ones are being planned by cybercriminals and nation-states.
Both proactive and reactive cyber defense efforts have advanced over the past two decades, but have so far failed to stem the tide of increasingly serious and more frequent attacks. The efforts have contributed to rapid growth of the cybersecurity industry (see Fig. V.1) and of the bounties paid to hackers for exploits attacking ever-more-secure and ever-more-complicated software.

Trustworthy Computing:
The first of the major software companies to shift corporate priorities in recognition of growing cyber threats and government pressure was Microsoft. Vulnerabilities in somewhat slapdash Microsoft software, including the Windows operating systems, for personal computers were among the most easily and frequently exploited in the 1990s and the first two years of the 21st century. The Internet Explorer browser Microsoft rather quickly and belatedly developed to compete with Netscape was an especially ripe target. Between 1999 and 2002 serious viruses and worms named Code Red, Melissa, ILOVEYOU, Nimda and Klez crippled millions of computers and networks running Microsoft software. Even White House computers were targets of attack. The FBI and the Pentagon suspected that some of these attacks were the work of cyber terrorists, and after 9/11 they made clear to Microsoft leaders that they needed to take security much more seriously.
On January 15, 2002 Bill Gates wrote an internal memo to Microsoft staff asserting that “Trustworthy computing is more important than any other part of our work” and that thenceforth security, privacy, reliability and business integrity would be the company’s highest priorities. Despite much initial skepticism from the hacker community, the priority change took hold. A book entitled Writing Secure Code, authored by Microsoft staff members Michael Howard and David LeBlanc, became a blueprint for a massive overhaul of most Microsoft products. The company began their now longstanding practice of releasing monthly software patches to all users. They initiated procedures to embrace (but not yet pay) the hacking community, setting up a customer service line for hackers to report vulnerabilities they’d discovered. And they began sharing their best practices and free resources with the rest of the industry, so that a decade later a Forbes article was happy to claim that “the business world owes a lot to Microsoft Trustworthy Computing.”
But improved software is still far from vulnerability-free. The Microsoft initiative ratcheted up the level of challenge involved in finding zero-day exploits in Microsoft software, but it did not diminish the number of hackers worldwide willing to take up that challenge. It also led to dramatic increases in the bounties brokers, cybercriminals and government agencies were willing to pay for critical exploits. Some sense of the bounty inflation accompanying improved software security can be gleaned from Fig. V.2, which shows the cumulative prices paid, as a function of time from first release, for zero-day exploits in four successive, and presumably increasingly secure, versions of Windows operating software. The most recent version, Windows 10, is presumably the most secure but is also the version fastest to reach a cumulative exploit expenditure of $28 million, simply because the bounty paid for each exploit has risen so rapidly throughout the past decade.

And despite Microsoft’s best efforts, Windows vulnerabilities have still formed critical parts of some of the major nation-state cyber attacks we reviewed in Part II of this post: Stuxnet, WannaCry and NotPetya. In the wake of the Shadow Brokers’ worldwide dump of parts of the NSA exploit stockpile in 2016-17, many attacks continue to this day using legacy Microsoft vulnerabilities, ones previously patched in past Microsoft software updates. This is possible because many users – including operators of critical infrastructure installations — continue to use outdated operating systems that Microsoft stopped supporting years ago, or are very slow to adopt security patches for more modern versions, out of concern that the software updates might disrupt smooth operations.
Publicizing Vulnerabilities and Supporting “Ethical” Hacking:
A number of the other major software development companies followed Microsoft’s lead during the first decade of this century to write less vulnerable code and combat cybercrime attacks. But they were not yet prepared to deal with the more sophisticated exploits gathered up by nation-states. The next milestone in upping software security came at the tail end of that first decade when, as we described in Part II, a fast-moving invasion of Google’s internal network was discovered and subsequently traced, with the aid of the cybersecurity companies Mandiant and McAfee, to hackers working for the Chinese government. The attack operation, dubbed Aurora, turned out to have infected networks at multiple Silicon Valley companies, in addition to other high-tech corporations, defense contractors, and financial services giants. Aurora was a sophisticated, multi-pronged cyber-espionage operation that gave the Chinese hackers access to source code repositories, from which they could in principle corrupt software used by millions of customers. Their goal at Google appears to have been gaining long-term access to any Gmail account they chose, and particularly those of activists they viewed as Chinese dissidents.
On January 12, 2010 Google forever changed the level of cybersecurity concerns by publishing a blog post openly accusing China of cyber theft of Google’s intellectual property. In the aftermath of Aurora, Google greatly expanded its own internal cybersecurity team and started paying volunteer hackers bounties for the zero-day vulnerabilities they were willing to share, all in service of a new mission to “neuter the world’s stockpiles of zero-day exploits and cyberweapons.” They began by paying hackers anywhere from $500 to $1,337 to turn over exploitable bugs, and soon raised the maximum payout to $31,337 (the succession of digits representing “eleet” in hacker code). Over the next few years, Facebook and Microsoft also joined the bug bounty game. But the payouts the software companies were willing to make paled in comparison to those offered by black market brokers and government agencies, so they had access only to a portion of the hacking community. Microsoft began paying hackers to uncover bugs in beta versions of their software products, before their public release, in order to avoid direct competition with the brokers.
The next shoe to drop came with Edward Snowden’s leaks of NSA documents in 2013. These revealed that, in addition to Microsoft and other tech companies occasionally complying with narrow, court-ordered requests to share customer accounts and metadata with NSA when these were germane to spying on targeted foreign terrorists, the NSA had been using its own zero-day exploits to hack into Google and Yahoo internal data centers. Those hacks, unbeknownst to the tech companies, had allowed the NSA to intercept customer e-mails and data before they were encrypted to transmit across the worldwide web. Those intercepts allowed the NSA to spy not only on U.S. citizens, but even on the leaders of foreign allies, such as Angela Merkel. The Snowden leaks caused the Obama administration considerable embarrassment and imposed strong international pressure on Google, Apple and other tech companies to make their systems harder to penetrate.
After the Snowden leaks Google began to encrypt all of its data internally, so that it could no longer be intercepted prior to encryption. Other companies followed suit, moving to a stronger form of encryption that greatly complicated decoding for NSA or other spying agencies. Apple introduced its iPhone 6 with complete encryption unlockable only by a user with password access to the phone, and software to wipe the phone’s data if a hacker entered ten incorrect passwords in succession. And in 2014 Google launched a new initiative, named Project Zero, with the goal of bringing to zero the number of critical bugs not only in its own software, but also in third-party code upon which Google systems relied. The Project Zero team partially adopted the typical hacker’s goal of attacking the weakest link in a chain, by searching for vulnerabilities easiest to repair in the zero-day exploit chains that nation-state hackers often applied in sophisticated attacks. The team gave other software vendors 90 days notice to patch the vulnerabilities they uncovered before they would publish information about the bugs and how they might be exploited online.
By publicizing their finds, the Project Zero team not only sent a message to potential customers about Google’s seriousness concerning cybersecurity, but also managed to attract at least some top exploit developers to move away from the “dark side” and join the defense team. To quote Nicole Perlroth: “Over the next few years, Project Zero identified more than sixteen hundred critical bugs, major flaws not just in the world’s most targeted software and security tools but also in the Intel chips inside nearly every computer in the world. Its researchers eliminated entire classes of bugs, making spies’ jobs a heck of a lot harder.”
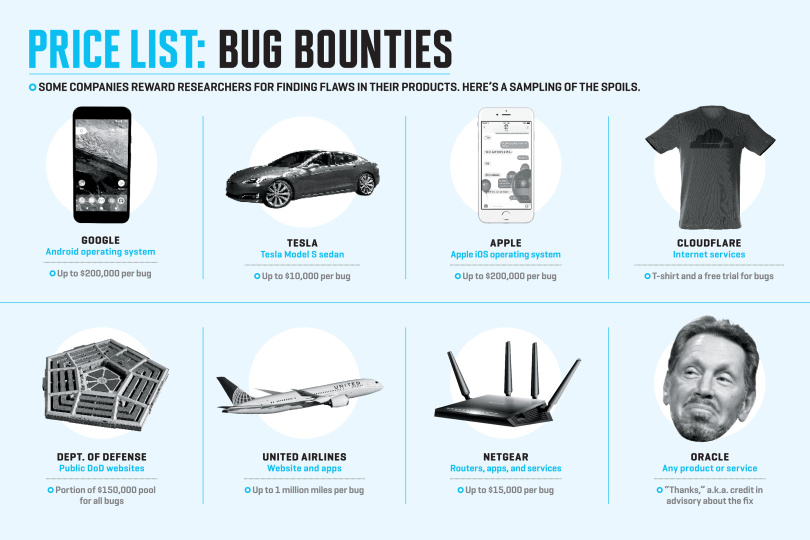
Project Zero continues to this day and represents one of the most aggressive and effective approaches yet to proactive cyber defense. About the same time that Google launched Project Zero, a team from the commercial company HackerOne recognized, and attracted venture capital for, a productive business model in managing bounty programs for as many companies and agencies as they could sign up. By now HackerOne serves as the middleman for negotiating and processing bounties to hackers from some of the major corporations in information technology, banking and financial services, telecommunications, automobile manufacturing, airlines and the oil industry. HackerOne advertises that: “The positive power of a community of ethical hackers pools our defenses against data breaches, reduces cybercrime, protects privacy, and restores trust in our digital society. Over 600,000 ethical hackers have willingly signed up with HackerOne to help our customers solve their greatest security challenges.” HackerOne soon attracted competitors in hacker bounty management, such as Bugcrowd and Synack. The bounties offered by different companies span a wide range, as illustrated in Fig. V.3 from a 2017 Fortune Magazine article.
The U.S. Government’s Role in Cyber Defense:
The most surprising customer of these bounty management companies is the U.S. Pentagon. At the same time that the NSA was continuing to invest heavily in discovering unknown zero-day vulnerabilities and developing offensive cyber exploits, the Obama administration recognized the deep holes in its cyber defense when it found in 2015 that Chinese hackers had almost a year earlier penetrated deeply within the computer systems of the Office of Personnel Management, containing sensitive personally identifying data for millions of federal employees and contractors. Cybersecurity and user alertness were also found to be inadequate in a number of other critical agencies, including the Internal Revenue Service, the Nuclear Regulatory Commission, the Securities and Exchange Commission and the Department of Education. President Obama had named a White House cybersecurity czar, although that office was subsequently eliminated by President Trump. But vulnerabilities in Defense Department critical software were especially worrisome, as they could allow adversaries to intercept mission-critical information or take over control of aircraft in flight. By 2018 the Department of Defense was investing $34 million into its managed hacker bounty program, a number still dwarfed by cyber offense expenditures at NSA.
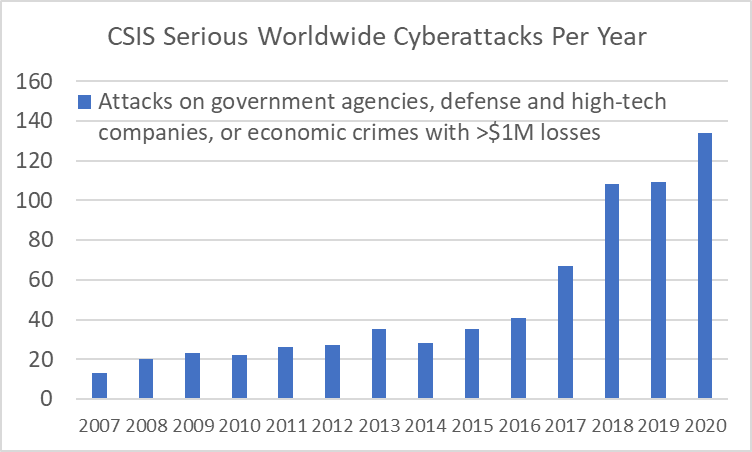
Google’s Project Zero and the “ethical” hacker bounties impeded, but certainly did not terminate, cybercrime, cyber-espionage and cyberwar. The growing trend can be seen in Fig. V.4 which includes the yearly totals from 2007 through 2020 of serious worldwide cyberattacks on government agencies, defense and high-tech companies, and cybercrimes causing economic losses in excess of one million U.S. dollars, as tracked by the Center for Strategic and International Studies. The recent rapid increases seen in the figure may arise in small part from more systematic reporting of such attacks. But the upward trend for 2017 and beyond can be primarily attributed to the Shadow Brokers leaks of NSA exploit code in 2016-17, to which we will return below. And the rising trend is predicted to continue as more hackers use artificial intelligence to scale up their attacks and begin to penetrate cloud systems where an increasing fraction of the world’s data is stored.
One problem was that the vulnerabilities Project Zero found were not always patched, or patched successfully, by the software vendors before information about the bugs was made public. Some of the vulnerabilities were found in open-source software that was very widely used, but had minimal technical support. A classic case is the Heartbleed bug revealed in 2014 in OpenSSL, an open-source software tool with worldwide applications to encrypt internet traffic. The bug allowed cyber- criminals to intercept and steal confidential data, including passwords and personal identity information. Despite its critical role in millions of internet-connected systems, OpenSSL was maintained by a single engineer in England who had almost no budget. Nonetheless, a patched version of OpenSSL was made available the same day the Heartbleed bug was publicized. But many system administrators have been very slow to adopt the updated version of OpenSSL, so that even five years after the fix nearly 100,000 internet-connected devices were found to be still vulnerable to the Heartbleed bug.
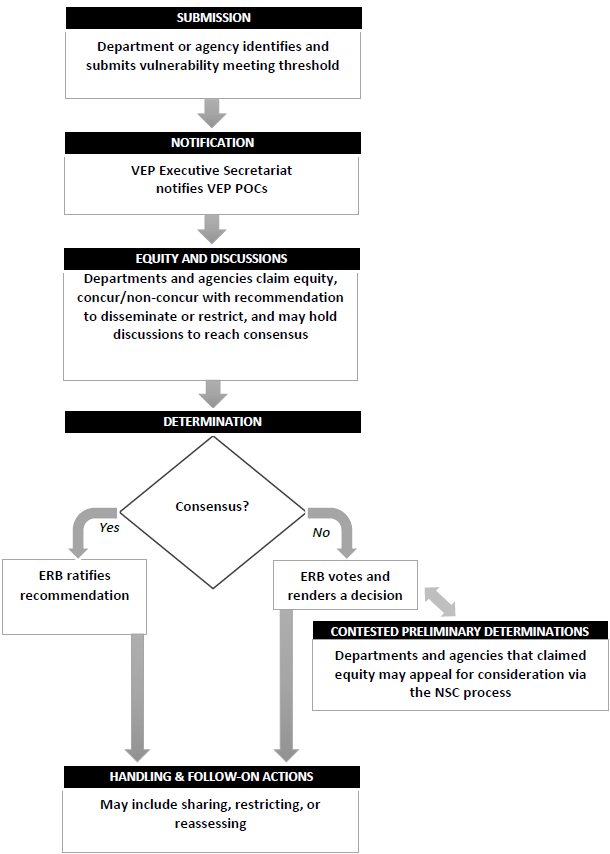
Bloomberg News used anonymous sources to report in 2014 that the NSA had known about the Heartbleed bug for two years before it was made public, but had kept it hidden in order to exploit it to gather critical intelligence. Although the NSA denied it, this claim did help to stimulate the Obama administration to take seriously a recommendation from the previous year that had been made by the National Intelligence Review Group on Intelligence and Communications Technologies. The Review Group had asserted that “in almost all instances, for widely used code, it is in the national interest to eliminate software vulnerabilities rather than to use them for US intelligence collection.” They argued that decisions about whether or not to withhold government-developed or government-purchased exploit information from the responsible software suppliers should be moved from the NSA to the White House. Such decisions, attempting to weigh the benefits of disclosure against those of maintaining secret offensive cyberweapon capabilities, are now made via a so-called Vulnerabilities Equities Process (VEP) considered by an Equities Review Board (ERB) comprising representatives of the potentially affected federal departments and agencies.
The existence of the VEP and ERB was first revealed to the public only in 2016-17, as NSA exploits started boomeranging back against the U.S. in the wake of the Shadow Brokers’ release of NSA stockpiles of exploit code. A statement posted to the White House website listed questions the ERB addresses in making its decisions, including: “Does the vulnerability, if left unpatched, impose significant risk? How much harm could an adversary nation or criminal group do with knowledge of this vulnerability? How likely is it that someone else will discover the vulnerability?” The broad outline of VEP procedures was summarized in the flow chart shown in Fig. V.5. But the Shadow Brokers’ leaks made clear that, despite government claims to the contrary, the VEP still favored offense over defense and overestimated the NSA’s ability to keep its own secrets.
The worldwide ransomware attack dubbed WannaCry (see Part II of this post) released by North Korea in 2017 spread so rapidly by relying on a stolen NSA exploit called EternalBlue. This was an exploit based on a zero-day vulnerability in Microsoft software that NSA hackers had relied on for seven years prior to the Shadow Brokers incident as a secret espionage tool to burrow into and move from targeted server to server without detection. If not for the worldwide leak of NSA exploits, they might never have alerted Microsoft to the vulnerability and its potential exploitation for cyberweapons of mass destruction. It was in fact used, along with another stolen NSA exploit, for just such a purpose in the subsequent NotPetya cyberattack perpetrated by Russia.
The Shadow Brokers’ leaks also revealed an exploit NSA held secret for four years in Oracle software affecting many of the world’s most widely used database systems. The Trump administration’s official responses to attacks utilizing stolen NSA exploits amounted to saying that they were not responsible for how others might choose to use tools developed by the U.S. But the government was certainly responsible for not alerting the software vendors much earlier so they could patch the vulnerabilities and limit worldwide damage from future cyber attacks.
User Responsibilities:
Cyber defense faces many challenges beyond nation-states hoarding offensive exploits. For as many bugs and vulnerabilities that have already been identified and patched, there must be many more lurking in the multiple billions of lines of code on which the world’s communications, controls and infrastructure now rely, still waiting to be discovered or held in stockpiles at government intelligence agencies. And new software with new vulnerabilities is emerging all the time, in part to control a rapidly expanding array of computer-controlled devices in the Internet of Things.
Some exploits have been implanted in the software updates intended to patch previously identified problems, as was the case for the 2020 SolarWinds attack, or to update malware protection. And many users leave their systems and networks vulnerable by failing to update software promptly to apply the newest security patches. Although they had waited seven years to do so, the NSA had alerted Microsoft to the bug behind the EternalBlue exploit a few weeks before the Shadow Brokers’ leak, and the company had in fact issued a patch for the bug two months prior to the WannaCry ransomware attack. Nonetheless, the attack wormed its way rapidly around the world because so many Microsoft users had not yet incorporated that patch in their systems.
Furthermore, well-hidden exploits can be challenging even for reactive defense efforts. When the best nation-state hackers want to implant themselves in adversaries’ systems without attracting attention, in preparation for gradual or later hijacking of control, the exploits can be difficult to detect. This has been the case for both the U.S. implementation of Stuxnet within Iran’s Natanz nuclear plant and the Russian attack on U.S. networks via SolarWinds, both of which were detected and traced only many months after the attacks were launched, and then only by accident.
But the weakest link in cyber defense still often comes down to inattentive system administrators or individual users. Too much of our critical infrastructure and voting platforms utilize outdated software that is no longer supported by its suppliers. Too many companies never bother to change passwords on their servers and devices from factory settings. Too many organizations have not yet adopted dual factor authentication, leaving their networks vulnerable to invasion via a single user who chooses an easy-to-crack password, or who uses the same password on multiple other accounts which might be penetrated to steal passwords.
An individual user can facilitate invasion by unwittingly clicking on a malicious attachment or link in a spear-phishing e-mail. This is how the Russian hacking group known as Fancy Bear had managed to gain access to all the e-mails of Hillary Clinton’s Presidential campaign manager John Podesta prior to the 2016 election. Podesta had received a purported Google security alert on his gmail account and, following best practices, forwarded the message to the Democratic National Committee’s security team for evaluation. The campaign aide who responded wrote “This is a legitimate email,” while later asserting that he had meant to write “illegitimate.” And with that slip of the keyboard, the campaign emails were stolen, weaponized, released by Wikileaks as an “October Surprise,” and may have helped to alter the course of history.
The U.S. government has not provided the level of support needed to make our cyber defenses more robust. The Trump administration eliminated the position of National Cybersecurity Coordinator in 2018. Congress has failed to pass meaningful legislation that might require companies managing critical infrastructure to adhere to basic minimal cybersecurity standards. The NSA appears to have decided that the best defense is an aggressive offense relying on winning the cyber arms race. A bipartisan bill introduced in 2017 – the PATCH (Protecting our Ability to Counter Hacking) Act – would have required Congressional oversight of the Vulnerabilities Equities Process and of its periodically reevaluated criteria and decisions. But the bill did not pass the Senate.
The minimal U.S. government support can be contrasted with that in various other countries that do not retain the goal of winning a cyberwar. For example, Nicole Perlroth highlights the situation in the highly digitized country of Norway: “Norwegians implemented a national cybersecurity strategy in 2003 and they revisit and update it every year to meet current threats. Norwegian companies that provide ‘basic national functions’ – financial services, electricity, health services, food supply, transportation, heating, media platforms, and communications – are required to have a ‘reasonable’ level of security. The government penalizes companies that do not perform penetration testing, threat monitoring, or adhere to other best security practices. Government employees are required to use electronic IDs, multifactor authentication, and encryption. And Norwegian corporations have made cyber-security core to their training and corporate culture.”
VI. Mutually assured cyber destruction
The main takeaway message from Sections IV and V of this post has been concisely summarized by Isaac Porche in a RAND Corporation blog: “Offensive cyber operations maintain the advantage over (largely) defensive operations due to the element of surprise and the pace of technological refresh that continues to create new backdoors.” Recognition of this state of affairs has convinced major nation-states that they need to make it clear to adversary states just how much offensive damage they could inflict on others’ critical infrastructure if anyone launches all-out cyber warfare. The messages are being delivered via mutual intrusion into each other’s control system networks.
A 2019 Axios report describing recent U.S. cyber incursions into controls and communications systems within Russia and Iran referred to the situation as “a lower-level 21st century version of the ‘mutually assured destruction’ policy between the U.S. and the Soviets that prevailed during the Cold War.” That Cold War standoff relied on both the U.S. and the Soviet Union having sufficient nuclear weapon stockpiles, sufficiently dispersed around the respective countries, that if either country chose to launch a first strike, the other could detect it and launch a retaliatory strike before the initial targets were hit.
The 21st century cyber warfare version of this philosophy differs in several important ways from the U.S.-U.S.S.R. nuclear stalemate. Perhaps the most important difference is the number of players. The weapons have already proliferated, offensive cyberwar capabilities are not that expensive to acquire, and many nation-states are “in the game.” The five current major players are summarized in Fig. VI.1.

In 2013 Iranian hackers, in retaliation for the U.S. Stuxnet attack on their uranium enrichment centrifuges, had demonstrated their ability to take over the Programmable Logic Controllers (PLCs) operating U.S. dams. The CIA was highly alarmed at the time because they were told the Iranian breach was of the Bowman Dam. But it was not, in fact, the Arthur B. Bowman Dam in Oregon, whose opening could have rapidly flooded 10,000 residences, but rather the tiny Bowman Avenue Dam in Westchester County, New York. Nonetheless, the message was received and then amplified two months later when Iran disabled most of the servers and wiped the hard drives clean at Sheldon Adelson’s Las Vegas Sands Corporation, the world’s largest gaming company, which operates casinos in Las Vegas, Macao, Singapore, and Bethlehem, Pennsylvania.
While Iran largely ceased aggressive cyber attacks on the U.S. after the Obama administration negotiated the Iran Nuclear Agreement in 2015, it has resumed offense in the wake of Trump’s withdrawal from that agreement and subsequent 2020 drone strike assassination of General Qassim Suleimani. Iranian hackers are currently embedded within the control systems for much of the American electrical grid and have penetrated computer systems within the Department of Energy and the national laboratories it funds, along with various oil and gas companies.
In 2013-14 Russian state hackers compromised industrial control software updates to infiltrate the control systems for a wide variety of U.S. critical infrastructure, including oil and gas pipelines, nuclear power plants, hydroelectric dams, water treatment facilities, and the American electrical grid. While they have not yet unleashed the capabilities they attained to deny power to many millions of Americans, the Russians have clearly demonstrated what they could do on their neighbor Ukraine. As we described in Part II of this post, Russian hackers famously shut down the electrical grid in Kyiv for six hours in late December 2015 to show the Ukrainians who was really in charge. They reinforced that message with the 2017 NotPetya attack, which shut down computers throughout Kyiv, including those governing airport controls, shipping, ATMs, banks, railways, bus stations, the postal service, media companies, and others. But NotPetya also traveled well beyond Ukraine to disable systems around the world. In addition, Russian state hackers have clearly shown their interest in sowing discord about democratic elections in a number of Western countries, prominently including the U.S., by spreading disinformation on social media and attacking computer systems that govern voter registration databases and voting platforms.
China has used its hackers in operations against the U.S. to date primarily for espionage, stealing industrial and government secrets, penetrating the government’s Office of Personnel Management, and spying on Tibetans and members of its Uighur Muslim minority and any visitors to websites supportive of the Uighur cause. But China maintains its own stockpile of zero-day exploits that are capable of much worse damage to U.S. critical infrastructure. North Korea has so far used its hacking capabilities mostly for bank heists and ransomware, like the WannaCry worldwide worm reliant on NSA exploit code released by the Shadow Brokers, to help fund its government’s ambitions.
The U.S. Cyber Command – the Defense Department organization started by the Obama administration to deploy cyber attacks – has responded in kind. In a classified program code-named Nitro Zeus they implanted cyber “time bombs” with capabilities to “disable Iran’s air defense, communication systems and crucial parts of its power grid,” starting during Obama’s second term as President, in case the Iran nuclear dispute led to conflict. In 2018 President Trump ceded decision-making about cyber attacks to the Director of NSA and Cyber Command, General Paul Nakasone. Cyber Command had already penetrated servers at the Internet Research Agency that had been responsible for Russian hacking and disinformation campaigns during the 2016 election, and took those servers offline on midterm Election Day and for several days thereafter in November 2018. And in 2019 the New York Times reported that the U.S. has placed “potentially crippling malware inside the Russian [electric] system at a depth and with an aggressiveness that had never been tried before.” The National Security Council backed up the latter Times story, no doubt wanting the Russians to know that they were vulnerable to a U.S. cyber attack. But President Trump called the report a “virtual act of treason,” continuing his ongoing avoidance of any signs of conflict with Russia and Vladimir Putin.
Although we have highlighted above bilateral attacks between the U.S. and each of the four other major nation-state combatants in the ongoing cyberwar, the capabilities are much more widely spread and applied. In a 2015 article, the Wall Street Journal reported that “at least 29 countries have formal military or intelligence units dedicated to offensive hacking efforts.” For example, Australia considers itself “at the forefront globally in acknowledging its offensive cyber capability and has used that capacity to target Islamic State and other threat actors.” Other examples can be gleaned from the following small sampling of incidents from the 82 major worldwide cyber attacks tracked by the Center for Strategic and International Studies over just the past six months:
- September 2020. The FBI and CISA (Cybersecurity and Infrastructure Security Agency) announced that Iranian hackers had been exploiting publicly known vulnerabilities to target U.S. organizations in the IT, government, healthcare, finance, and media sectors.
- September 2020. Russian hackers targeted government agencies in NATO member countries, and nations who cooperate with NATO. The campaign uses NATO training material as bait for a phishing scheme that infects target computers with malware that creates a persistent backdoor.
- October 2020. U.S. government officials revealed that suspected Chinese hackers were behind a series of attacks on entities in Russia, India, Ukraine, Kazakhstan, Kyrgyzstan, and Malaysia.
- October 2020. Iran announced that the country’s Ports and Maritime Organization and one other unspecified government agency had come under cyber attack.
- October 2020. The UK’s National Cybersecurity Centre found evidence that Russian military intelligence hackers had been planning a disruptive cyber attack on the later-postponed 2020 Tokyo Olympics.
- October 2020. A North Korean hacker group carried out attacks against aerospace and defense companies in Russia.
- November 2020. Chinese hackers targeted Japanese organizations in multiple industry sectors located in multiple regions around the globe, including North America, Europe, Asia, and the Middle East.
- December 2020. Over 200 organizations around the world including multiple US government agencies were revealed to have been breached by Russian hackers who compromised the software provider SolarWinds and exploited their access to monitor internal operations and exfiltrate data.
- December 2020. Unknown state-sponsored hackers took advantage of territory disputes between China, India, Nepal, and Pakistan to target government and military organizations across South Asia, including the Nepali Army and Ministries of Defense and Foreign Affairs, the Sri Lankan Ministry of Defense, and the Afghan National security Council and Presidential Palace.
- January 2021. Suspected Indian hackers active since 2012 attacked business and governments across South and East Asia, with a particular emphasis on military and government organizations in Pakistan, China, Nepal, and Afghanistan, and businesses involved in defense technology, scientific research, finance, energy, and mining.
- February 2021. Unknown hackers attempted to raise levels of sodium hydroxide in the water supply of Oldsmar, Florida by a factor of 100 by exploiting a remote access system.
- February 2021. Iranian hackers took control of a server in Amsterdam and used it as a command and control center for attacks against political opponents in the Netherlands, Germany, Sweden, and India.
- February 2021. Russian hackers compromised a Ukrainian government file-sharing system and attempted to disseminate malicious documents that would install malware on computers that downloaded the planted files.
- February 2021. North Korean hackers targeted defense firms in more than a dozen countries in an espionage campaign starting in early 2020.

In addition to the expanded number of nation-states engaged (see Fig. VI.2), the current cyber warfare situation differs significantly from the Cold War nuclear standoff because cyber attacks are survivable. They have the capability to cause major disruption, disinformation, chaos, pain and deaths, but in all probability targeted nations can recover even from extended breaches of their critical infrastructure. This realization reduces the deterrence power of a possible counter-attack from a targeted nation and therefore reduces the impetus for all of the affected nations to enter into treaties restricting the offensive uses of cyberweapons. In any case, it is much more challenging to negotiate such treaties among tens of nations than between two primary combatants. And the more nations that are involved in an arms race, the more likely it is to have warfare eventually triggered by accident or by the actions of an irrational leader.
One further difference from the nuclear standoff may serve as a cautionary element damping enthusiasm for launching all-out cyber warfare. That is the “boomerang” effect. A cyberweapon launched by a nation-state can come back to invade the aggressor’s own computer systems. This possibility was already made clear when the Stuxnet worm leaked beyond the targeted systems in Iran, though in that case the targeting was so specific to the Natanz facility’s centrifuge configuration that the invasion was harmless in other countries. It was demonstrated more pointedly in the NotPetya attack in 2017. Russian state hackers targeted the attack on Ukrainian systems, but it spread rapidly across the internet to Copenhagen, the U.S., China, Tasmania and even back to Russia, where it disabled computers at the Russian oil giant Rosneft. The uncertainty in predicting just what weaponized malware will do in an interconnected world has led one NATO researcher, Matthijs Veenendaal, to suggest that the acronym MAD, which stood for “mutually assured destruction” during the Cold War, should now be interpreted as “mutually assured doubt.”
VII. how do we move forward?
So how can we navigate through this fraught array of cocked cyberweapons? There have been a few overtures toward limited bilateral “peace treaties.” In 2015 the U.S. and China announced an agreement “not to direct or support cyberattacks that steal corporate records for economic benefit.” But, as the Wall Street Journal article reporting the agreement pointed out, “it was unclear how the agreement will be enforced or whether it will prompt a meaningful change in a behavior that Chinese leaders have long denied.” In the weeks leading up to the 2020 U.S. Presidential election, Vladimir Putin appealed to the U.S. “to reset our relations in the use of information and communication technologies,” specifically “exchanging guarantees of non-interference in each other’s internal affairs, including electoral processes.” But predictably, American officials dismissed Putin’s call as self-serving propaganda.
There have been suggestions for a digital counterpart to the Geneva Convention for traditional warfare, declaring certain targets off-limits for cyber attacks, such as hospitals, election infrastructure, airplanes and nuclear facilities. Such an agreement might be difficult to enforce for several reasons: a number of the major nation-state players – prominently including Russia, China and Iran – often outsource their cyber attacks to cyber criminals and mercenary hackers who would not be bound by any such convention; and the off-limit infrastructure might still suffer severe collateral damage from a computer worm that propagates far beyond the aggressor’s originally intended target.
But there have been some promising initial efforts to at least interpret constraints on cyber warfare imposed by existing industrial-age international law. These began with a study sponsored by the NATO Cooperative Cyber Defence Centre of Excellence (CCDCOE), leading to publication in 2013 of an academic, non-binding report referred to as the Tallinn Manual. The applicability of international law was confirmed in 2013 by the United Nations Group of Governmental Experts (UN GGE) on Developments in the Field of Information and Telecommunications in the Context of International Security. The UN GGE was reconvened in 2015, with the group comprising representatives from 20 countries, including key cyber powers such as the U.S., China, Russia, France, the UK and Germany. The 2015 consensus report, endorsed by all members of the UN General Assembly, put forth a set of norms and good practices to serve as a basis for responsible nation-state behavior in cyberspace. Some examples of the proposed norms are as follows:
- States should not conduct or knowingly support ICT (information and communications technologies) activity that intentionally damages critical infrastructure.
- States should take steps to ensure supply chain security, and should seek to prevent the proliferation of malicious ICT and the use of harmful hidden functions.
- States should not conduct or knowingly support activity to harm the information systems of another state’s emergency response teams and should not use their own teams for malicious international activity.
- States should respect the UN resolutions that are linked to human rights on the internet and to the right to privacy in the digital age.
- States should consider how best to cooperate to exchange information, to assist each other, and to prosecute terrorist and criminal use of ICTs.
- States should encourage responsible reporting of ICT vulnerabilities and should share remedies to these.
Although Russian and Chinese representatives co-authored the UN GGE report, it did not go as far as those countries would have preferred toward establishing new international laws specifically governing ICT, together with “a democratic and multilateral internet management system.” Together with Kazakhstan, Kyrgyzstan, Tajikistan and Uzbekistan, Russia and China put forward their own proposals in a 2015 Shanghai Cooperation Organization (SCO) document. The SCO report emphasizes “respect for sovereignty and territorial integrity” in cyberspace, which some see as a veiled way of legitimizing censorship and state control over the internet. Western powers seem to be specifically targeted in other SCO language, urging each signatory of a UN agreement “not to take advantage of its dominant position in the sphere of information technology … to undermine other countries’ right of independent control of ICT products and services, or to threaten other countries’ political, economic and social security.” The U.S. and allies have also argued that new international laws are not needed and might limit technological innovation and growth.
The failure of the UN to adopt their preferred language about not taking advantage of a “dominant position in the sphere of information technology” has led Russia and China to work assiduously and successfully since 2015, with some help from the Shadow Brokers’ leak of NSA exploit code, to overcome what they may have seen as their earlier shortcomings. They have both demonstrated their enhanced capabilities in prominent penetrations of U.S. and other western country networks. So have Iran and North Korea. This situation has led a consortium of 28 nations to issue a Joint Statement on Advancing Responsible State Behavior in Cyberspace in September 2019. The countries supporting the statement are: Australia, Belgium, Canada, Colombia, the Czech Republic, Denmark, Estonia, Finland, France, Germany, Hungary, Iceland, Italy, Japan, Latvia, Lithuania, the Netherlands, New Zealand, Norway, Poland, the Republic of Korea, Romania, Slovakia, Slovenia, Spain, Sweden, the United Kingdom, and the United States.
The 2019 Joint Statement summarizes the problem more pointedly than the UN reports:
“State and non-state actors are using cyberspace increasingly as a platform for irresponsible behavior from which to target critical infrastructure and our citizens, undermine democracies and international institutions and organizations, and undercut fair competition in our global economy by stealing ideas when they cannot create them.”
It also emphasizes the need for consequences:
“As responsible states that uphold the international rules-based order, we recognize our role in safeguarding the benefits of a free, open, and secure cyberspace for future generations. When necessary, we will work together on a voluntary basis to hold states accountable when they act contrary to this framework, including by taking measures that are transparent and consistent with international law. There must be consequences for bad behavior in cyberspace.”
What might those consequences entail? James A. Lewis, a respected expert on cybersecurity, technology and international cyber strategy, argues in recent remarks to the U.S. Cyber Command Legal Conference that the most effective and defensible consequences would target an adversary’s cyber capabilities: “Damaging the cyber infrastructure that provides an opponent the ability to engage in espionage or politically coercive actions is most likely to benefit the United States while minimizing the risk of escalation.” We already have seen a hint of that strategy in action when Cyber Command took servers at Russia’s Internet Research Agency offline on Election Day 2018. While Lewis argues that it is unlikely to have sufficient advance knowledge of imminent attacks to justify targeted preemptive action, he does support “attacking opponent cyber assets in an incremental and sequential manner to degrade their capability to attack the United States and its allies.”
Whether such a strategy in fact minimizes the risk of escalation is open to debate. Nation-state hackers work hard to hide their tracks, making clear attribution of the source of an attack subject to circumstantial evidence, and seldom agreed to by the indicated source. Countries denying responsibility for a cyber attack will assert their right to self-defense in responding to any “consequence” attack on their own cyber infrastructure, and are likely to return “fire” according to their own strategy. And again, it is challenging to assure limited targeting in cyber attacks; worms gonna worm through and across networks, often with unintended consequences.
Our short-term hopes thus rely on the numerous nation-states capable of destructive cyber warfare acting rationally, if not always responsibly – being constrained by clear-eyed assessments of likely responses to any attacks they might launch. But for the longer term, it seems essential to demand more of software and computer hardware security. In an era where we are capable of mapping the billions of base pairs in the human genome, why can’t we demand that software developers maintain clear and accurate accounts of the length of any code they write or use, so that malicious code implants can be detected instantaneously via unauthorized length changes? This would at least reduce the surface area susceptible to attack, limiting success to code implanted during development, as seems to have been done by the Russians for the SolarWinds software update. This would clearly require a major undertaking for all existing software, much of which is open source.
A reasonable first step would be requiring that all software applications be accompanied by a software bill of materials (SBOM), listing all components of the code, including open-source and third-party modules, version numbers, and patch status for all known earlier vulnerabilities in each component. Thanks especially to the efforts of Google’s Project Zero team and the ethical hackers working with industry, there is a well-developed database now listing the previously revealed vulnerabilities. Yet commercial software is particularly vulnerable to problems in open-source code components, as was the case in the Heartbleed bug exploited by cyber criminals. The Synopsys team reports that “Our audit services team found that 85% of the codebases we scanned in 2018 contained open source components that were more than four years out-of-date or had no development activity in the last two years.” And many of those out-of-date open-source modules were subject to known exploitable vulnerabilities. A striking example of the organic and often poorly controlled growth of code over time is presented by one product of the Chinese software company Huawei, which researchers have found to contain “79 different versions of the exact same encryption module…with many of the older versions vulnerable to the notorious Heartbleed hack from 2014.”
As in the case of manufacturing, a suitably detailed bill of materials allows a supplier not only to certify that a product is free from known defects, but also to track the source of any newly discovered defect and to report it promptly to both the component supplier for patching and to customers for alertness to potential problems. At the moment, however, there is no agreed-upon standard for SBOMs and a recent survey indicates that fewer than half of software application developers currently have the ability to produce a meaningful SBOM. In the wake of the Heartbleed exploits the U.S. Congress tried, but failed, to pass the 2014 Cyber Supply Chain Management and Transparency Act, which would have required all software and firmware purchased by government agencies to be accompanied by a clear bill of materials. The National Telecommunications and Information Administration within the U.S. Department of Commerce is currently working with industry to develop an SBOM standard. But government action does not seem essential here. If a majority of companies and institutions purchasing commercial software systems were to require an SBOM for each product they purchase, software developers would have to evolve the capability to produce them.
Security improvements also extend to computer hardware. Researchers at the University of Cambridge and SRI International have developed a new microchip architecture, which supports software compartmentalization to keep untrustworthy or malicious code from operating on the critical chips within computers and smart phones, and fine-grained protection to limit the ability of exploits to overwrite sensitive parts of computer memory. Work is underway to explore the possible adoption of this new technology in mass-market commercial processors.
The increasing frequency of serious worldwide cyber attacks seen in Fig. V.4 signals that it is past time to abandon Mark Zuckerberg’s mantra of “Move fast and break things,” and to demand that IT developers innovate to help protect all of us from potentially disastrous cyberspace weapons.
references:
N. Perlroth, This is How They Tell Me the World Ends: The Cyberweapons Arms Race (Bloomsbury Publishing, 2021), https://www.amazon.com/This-They-Tell-World-Ends/dp/1635576059/
A. Terekhov, The Cyber Black Market: A Hacker’s Haven, https://www.hotspotshield.com/blog/the-cyber-black-market/
Cyber Security Threats and Attacks: All You Need to Know, https://www.stealthlabs.com/blog/cyber-security-threats-all-you-need-to-know/
https://en.wikipedia.org/wiki/Nathaniel_Borenstein
https://en.wikipedia.org/wiki/Mark_Zuckerberg
H. Taneja, The Era of “Move Fast and Break Things” is Over, Harvard Business Review, Jan. 22, 2019, https://hbr.org/2019/01/the-era-of-move-fast-and-break-things-is-over
https://en.wikipedia.org/wiki/Internet_of_things
https://en.wikipedia.org/wiki/Market_for_zero-day_exploits
R. Arroyo, Mutually Assured Destruction, in Cyberspace?, https://www.secplicity.org/2019/11/12/mutually-assured-destruction-in-cyberspace/
https://en.wikipedia.org/wiki/Multi-factor_authentication
https://en.wikipedia.org/wiki/2015_San_Bernardino_attack
https://en.wikipedia.org/wiki/Edward_Snowden
E. Nakashima and R. Albergotti, The FBI Wanted to Unlock the San Bernadino Shooter’s iPhone. It Turned to a Little-known Australian Firm, Washington Post, April 14, 2021, https://www.washingtonpost.com/technology/2021/04/14/azimuth-san-bernardino-apple-iphone-fbi/
https://www.azimuthsecurity.com/
SolarWinds: How Russian Spies Hacked the Justice, State, Treasury, Energy and Commerce Departments, CBS “60 Minutes” segment, Feb. 14, 2021, https://www.cbsnews.com/news/solarwinds-hack-russia-cyberattack-60-minutes-2021-02-14/
The Threats Arising from the Massive SolarWinds Hack, CBS Sunday Morning, Jan. 3, 2021, https://www.youtube.com/watch?v=E390AhlOcSo
A. Roth, Biden to Unveil Russia Sanctions over SolarWinds Hack and Election Meddling, The Guardian, April 15, 2021, https://www.theguardian.com/us-news/2021/apr/14/biden-set-to-sanction-russian-officials-over-massive-solarwinds-hack
S. Morgan, Global Ransomware Damage Costs Predicted to Reach $20 Billion (USD) by 2021, Cybercrime Magazine, Oct. 21, 2019, https://cybersecurityventures.com/global-ransomware-damage-costs-predicted-to-reach-20-billion-usd-by-2021/
J. Davis, Update: UHS Health System Confirms All US Sites Affected by Ransomware Attack, Health IT Security, Oct. 5, 2020, https://healthitsecurity.com/news/uhs-health-system-confirms-all-us-sites-affected-by-ransomware-attack
S. Coble, Ransomware Disrupts COVID-19 Medical Trials, Infosecurity Magazine, https://www.infosecurity-magazine.com/news/ransomware-disrupts-covid19/
The Cyber Kill Chain, https://www.lockheedmartin.com/en-us/capabilities/cyber/cyber-kill-chain.html
G. Ratnam, Mueller Report: Russia Hacked State Databases and Voting Machine Companies, Roll Call, Apr. 22, 2019, https://www.rollcall.com/2019/04/22/mueller-report-russia-hacked-state-databases-and-voting-machine-companies/
Manipulated Data: The New Bank Hack, https://sqnbankingsystems.com/blog/manipulated-data-new-bank-hack/
https://en.wikipedia.org/wiki/December_2015_Ukraine_power_grid_cyberattack
C. Bing, Hackers Try to Contaminate Florida Town’s Water Supply Through Computer Breach, U.S. News, Feb. 8, 2021, https://www.usnews.com/news/us/articles/2021-02-08/hackers-broke-into-florida-towns-water-treatment-plant-attempted-to-poison-supply-sheriff-says#:~:text=Hackers%20Try%20to%20Contaminate%20Florida%20Town’s%20Water%20Supply%20Through%20Computer%20Breach
https://en.wikipedia.org/wiki/Stuxnet
M. Thompson, Iranian Cyber Attack on New York Dam Shows Future of War, Time Magazine, Mar. 24, 2016, https://time.com/4270728/iran-cyber-attack-dam-fbi/
How the Shadow Brokers Unleashed the NSA’s Powerful Cyberweapons on the World, https://cyberx-labs.com/blog/shadow-brokers-unleashed-nsas-powerful-cyberweapons-world/
https://en.wikipedia.org/wiki/The_Shadow_Brokers
https://en.wikipedia.org/wiki/Bugtraq
A. Litan, How to Make Russian Hacker Attribution Useful to Active Defense, Gartner, Mar. 28, 2017, https://blogs.gartner.com/avivah-litan/2017/03/28/how-to-make-russian-hacker-attribution-useful-to-active-defence/
L. Ablon, M.C. Libicki and A.M. Abler, Markets for Cybercrime Tools and Stolen Data, RAND Corporation Research Report, 2014, https://www.rand.org/pubs/research_reports/RR610.html
J.R. Gosler, U.S. Intelligence Transformation: The Digital Dimension, https://cisac.fsi.stanford.edu/events/us_intelligence_transformation_the_digital_dimension
D. Fisher, Chaouki Bekrar: The Man Behind the Bugs, https://threatpost.com/chaouki-bekrar-man-behind-bugs-030912/76312/
https://zerodium.com/program.html
https://en.wikipedia.org/wiki/Mass_surveillance_in_China
A. Mitchell and L. Diamond, China’s Surveillance State Should Scare Everyone, The Atlantic, Feb. 2, 2018, https://www.theatlantic.com/international/archive/2018/02/china-surveillance/552203/
https://en.wikipedia.org/wiki/Uyghurs
D. Davies, Facial Recognition and Beyond: Journalist Ventures Inside China’s ‘Surveillance State,’ NPR, Jan. 5, 2021, https://www.npr.org/2021/01/05/953515627/facial-recognition-and-beyond-journalist-ventures-inside-chinas-surveillance-sta
Out of Sight, Not Out of Reach: Understanding Transnational Repression, Freedom House publication, 2020.
M. Abramowitz and N. Schenkkan, The Long Arm of the Authoritarian State, Washington Post, Feb. 3, 2021, https://www-washingtonpost-com.proxyiub.uits.iu.edu/opinions/2021/02/03/freedom-house-transnational-repression-authoritarian-dissidents/?itid=lk_inline_manual_63
https://en.wikipedia.org/wiki/The_Interview
A.. Peterson, The Sony Pictures Hack, Explained, Washington Post, Dec. 18, 2014, https://www.washingtonpost.com/news/the-switch/wp/2014/12/18/the-sony-pictures-hack-explained/
Dradis Pro, Interview with Matthew Hickey [co-founder of Hacker House computer security firm], https://dradisframework.com/academy/interviews/hackerhouse-matthew-hickey.html
K. Zetter, Inside the Cunning, Unprecedented Hack of Ukraine’s Power Grid, Wired, Mar. 16, 2016, https://www.wired.com/2016/03/inside-cunning-unprecedented-hack-ukraines-power-grid/
A. Greenberg, Sandworm: A New Era of Cyberwar and the Hunt for the Kremlin’s Most Dangerous Hackers (Doubleday, 2019), https://www.amazon.com/Sandworm-Cyberwar-Kremlins-Dangerous-Hackers/dp/0385544405
N. Perlroth, M. Scott and S. Frenkel, Cyberattack Hits Ukraine Then Spreads Internationally, New York Times, June 27, 2017, https://www.nytimes.com/2017/06/27/technology/ransomware-hackers.html
K. Zetter, Countdown to Zero Day: Stuxnet and the Launch of the World’s First Digital Weapon (Broadway Books, 2015), https://www.amazon.com/Countdown-Zero-Day-Stuxnet-Digital/dp/0770436196
F. Kaplan, Dark Territory: The Secret History of Cyber War (Simon & Schuster, 2016), https://www.amazon.com/Dark-Territory-Secret-History-Cyber/dp/1476763267
A. Greenberg, The Untold Story of NotPetya, the Most Devastating Cyberattack in History, Wired, Aug. 2018, https://www.wired.com/story/notpetya-cyberattack-ukraine-russia-code-crashed-the-world/
E. Nakashima, Russian Military Was Behind ‘NotPetya’ Cyberattack in Ukraine, CIA Concludes, Washington Post, Jan. 12, 2018, https://www-washingtonpost-com.proxyiub.uits.iu.edu/national-security/russian-military-was-behind-notpetya-cyberattack-in-ukraine-cia-concludes/2018/01/12/048d8506-f7ca-11e7-b34a-b85626af34ef_story.html
D. Sanger, Confront and Conceal: Obama’s Secret Wars and Surprising Use of American Power (Broadway Books, 2012), https://www.amazon.com/Confront-Conceal-Obamas-Surprising-American-ebook/dp/B006LTIS7G
N. Perlroth, J. Larson and S. Shane, NSA Able to Foil Basic Safeguards of Privacy on the Web, New York Times, Sept. 5, 2013, https://www.nytimes.com/2013/09/06/us/nsa-foils-much-internet-encryption.html
C. Savage, Declassified Report Shows Doubts About Value of NSA’s Warrantless Spying, New York Times, Apr. 24, 2015, https://www.nytimes.com/2015/04/25/us/politics/value-of-nsa-warrantless-spying-is-doubted-in-declassified-reports.html
R. Bergman and M. Mazzetti, The Secret History of the Push to Strike Iran, New York Times, Sept. 4, 2019, https://www.nytimes.com/2019/09/04/magazine/iran-strike-israel-america.html
R. Bergman, R. Gladstone and F. Fassihi, Blackout Hits Iran Nuclear Site in What Appears to be Israeli Sabotage, New York Times, Apr. 11, 2021, https://www.nytimes.com/2021/04/11/world/middleeast/iran-nuclear-natanz.html
IAEA Says Inspectors ‘Are Continuing Their Verification and Monitoring Activities in Iran’ Days After Reported Attack on Facility, Times of Israel, Apr. 14, 2021, https://www.timesofisrael.com/un-nuclear-watchdog-inspects-irans-natanz-plant-after-explosion/
D. Sanger, The Perfect Weapon: War, Sabotage and Fear in the Cyber Age (Crown Publishing, 2018), https://www.amazon.com/Perfect-Weapon-Sabotage-Fear-Cyber/dp/0451497899
R. Gallagher and G. Greenwald, How the NSA Plans to Infect ‘Millions’ of Computers with Malware, The Intercept, Mar. 12, 2014, https://theintercept.com/2014/03/12/nsa-plans-infect-millions-computers-malware/
M. Mazzetti, A. Goldman, R. Bergman and N. Perlroth, A New Age of Warfare: How Internet Mercenaries Do Battle for Authoritarian Governments, New York Times, Mar. 21, 2019, https://www.nytimes.com/2019/03/21/us/politics/government-hackers-nso-darkmatter.html
D.E. Sanger and N. Perlroth, Hackers from China Resume Attacks on U.S. Targets, New York Times, May 19, 2013, https://www.nytimes.com/2013/05/20/world/asia/chinese-hackers-resume-attacks-on-us-targets.html
B. Johnson, Google Stops Censoring Chinese Search Engine: How It Happened, The Guardian, Mar. 22, 2010, https://www.theguardian.com/technology/blog/2010/mar/22/google-china-live
G. Greenwald and E. MacAskill, NSA Prism Program Taps Into User Data of Apple, Google and Others, The Guardian, June 7, 2013, https://www.theguardian.com/world/2013/jun/06/us-tech-giants-nsa-data
D. Sanger and N. Perlroth, U.S. Said to Find North Korea Ordered Cyberattack on Sony, New York Times, Dec. 17, 2014, https://www.nytimes.com/2014/12/18/world/asia/us-links-north-korea-to-sony-hacking.html
D.E. Sanger, M.S. Schmidt and N. Perlroth, Obama Vows a Response to Cyberattack on Sony, New York Times, Dec. 19, 2014, https://www.nytimes.com/2014/12/20/world/fbi-accuses-north-korean-government-in-cyberattack-on-sony-pictures.html
N. Perlroth and D.E. Sanger, Hackers Hit Dozens of Countries Exploiting Stolen NSA Tool, New York Times, May 12, 2017, https://www.nytimes.com/2017/05/12/world/europe/uk-national-health-service-cyberattack.html
D.E. Sanger, Shadow Brokers’ Leak Raises Alarming Question: Was the NSA Hacked?, New York Times, Aug. 16, 2016, https://www.nytimes.com/2016/08/17/us/shadow-brokers-leak-raises-alarming-question-was-the-nsa-hacked.html
B. Sterling, Shadow Brokers Manifesto, Wired, Aug. 19, 2016, https://www.wired.com/beyond-the-beyond/2016/08/shadow-brokers-manifesto/
T.P. Bossert, It’s Official: North Korea is Behind WannaCry, Wall Street Journal, Dec. 18, 2017, https://www.wsj.com/articles/its-official-north-korea-is-behind-wannacry-1513642537
B. Smith, The Need for Urgent Collective Action to Keep People Safe Online: Lessons from Last Week’s Cyberattack, Microsoft Blogs, May 14, 2017, https://blogs.microsoft.com/on-the-issues/2017/05/14/need-urgent-collective-action-keep-people-safe-online-lessons-last-weeks-cyberattack/
P. Mozur, One Month, 500,000 Face Scans: How China is Using A.I. to Profile a Minority, New York Times, Apr. 14, 2019, https://www.nytimes.com/2019/04/14/technology/china-surveillance-artificial-intelligence-racial-profiling.html#:~:text=the%20main%20story-,One%20Month%2C%20500%2C000%20Face%20Scans%3A%20How%20China%20Is%20Using,A.I.%20to%20Profile%20a%20Minority&text=Now%2C%20documents%20and%20interviews%20show,Uighurs%2C%20a%20largely%20Muslim%20minority
L. Columbus, 2020 Roundup of Cybersecurity Forecasts and Market Estimates, Forbes Magazine, Apr. 5, 2020, https://www.forbes.com/sites/louiscolumbus/2020/04/05/2020-roundup-of-cybersecurity-forecasts-and-market-estimates/?sh=6a3101f9381d
https://en.wikipedia.org/wiki/Code_Red_(computer_worm)
https://en.wikipedia.org/wiki/Melissa_(computer_virus)
https://en.wikipedia.org/wiki/ILOVEYOU
https://en.wikipedia.org/wiki/Nimda
https://en.wikipedia.org/wiki/Klez
https://en.wikipedia.org/wiki/Trustworthy_computing
M. Howard and D. LeBlanc, Writing Secure Code (Microsoft Press, 2003), https://www.amazon.com/Writing-Secure-Second-Developer-Practices/dp/0735617228
https://www.microsoft.com/en-us/securityengineering/sdl/
T. Bradley, The Business World Owes a Lot to Microsoft Trustworthy Computing, Forbes Magazine, Mar. 5, 2014, https://www.forbes.com/sites/tonybradley/2014/03/05/the-business-world-owes-a-lot-to-microsoft-trustworthy-computing/?sh=64ecee2959db
M. Ruef, Exploit Market Forecasts: A Glimpse Into the Future, https://www.scip.ch/en/?labs.20170209
https://www.fireeye.com/mandiant.html
https://www.mcafee.com/en-us/index.html
https://en.wikipedia.org/wiki/Operation_Aurora
https://en.wikipedia.org/wiki/Project_Zero
https://googleprojectzero.blogspot.com/
R. Hackett, Google’s Elite Hacker SWAT Team vs. Everyone, Fortune Magazine, June 23, 2017, https://fortune.com/2017/06/23/google-project-zero-hacker-swat-team/
https://www.hackerone.com/hack-for-good
https://www.bugcrowd.com/products/how-it-works/the-bugcrowd-difference/
https://en.wikipedia.org/wiki/Office_of_Personnel_Management_data_breach
Center for Strategic and International Studies, Significant Cyber Incidents Since 2006, https://csis-website-prod.s3.amazonaws.com/s3fs-public/210226_Significant_Cyber_Events.pdf?_zgMwQn.ZIQlHWCMGNMZfZJhjcypWe6s
S. Andriole, Cyberwarfare Will Explode in 2020 (Because It’s Cheap, Easy and Effective), Forbes Magazine, Jan. 14, 2020, https://www.forbes.com/sites/steveandriole/2020/01/14/cyberwarfare-will-explode-in-2020-because-its-cheap-easy–effective/?sh=41a39efc6781
https://en.wikipedia.org/wiki/Heartbleed
M. Riley, NSA Said to Have Used Heartbleed Bug, Exposing Consumers, Bloomberg News, Apr. 12, 2014, https://www.bloomberg.com/news/articles/2014-04-11/nsa-said-to-have-used-heartbleed-bug-exposing-consumers
https://en.wikipedia.org/wiki/Vulnerabilities_Equities_Process
G. Otto, White House Unveils Process Behind Disclosing Software Vulnerabilities, CyberScoop, Nov. 15, 2017, https://www.cyberscoop.com/vulnerabilities-equities-process-vep-charter-white-house-rob-joyce/
S. Cobb, US Vulnerabilities Equities Policy: Transparency Welcome, But Serious Questions Remain, https://www.welivesecurity.com/2017/11/15/us-vulnerability-equities-policy-questions-remain/
https://en.wikipedia.org/wiki/WannaCry_ransomware_attack
https://en.wikipedia.org/wiki/EternalBlue
https://en.wikipedia.org/wiki/Petya_(malware)
https://en.wikipedia.org/wiki/Fancy_Bear
https://en.wikipedia.org/wiki/Podesta_emails
PATCH Act of 2017, https://www.govtrack.us/congress/bills/115/hr2481/text
I.R. Porche III, Fighting and Winning the Undeclared Cyber War, RAND Blog, June 24, 2019, https://www.rand.org/blog/2019/06/fighting-and-winning-the-undeclared-cyber-war.html
S. LeVine, The U.S. Goes on the Cyber Offensive, Axios, June 19, 2019, https://www.axios.com/us-cyber-offensive-b56a4889-2748-485e-9b7f-d74cb0c0c605.html
D. Paletta, D. Yadron and J. Valentino-DeVries, Cyberwar Ignites a New Arms Race, The Wall Street Journal, Oct. 11, 2015, https://www.wsj.com/articles/cyberwar-ignites-a-new-arms-race-1444611128
C. Bennett, Iranian Hackers Downed Adelson’s Casino Empire, The Hill, Dec. 12, 2014, https://thehill.com/policy/cybersecurity/226915-iranian-hackers-downed-us-casino-empire
Who Are the Uighurs and Why is the U.S. Accusing China of Genocide?, BBC News, Feb. 9, 2021, https://www.bbc.com/news/world-asia-china-22278037
D.E. Sanger and M. Mazetti, U.S. Had Cyberattack Plan if Iran Nuclear Dispute Led to Conflict, New York Times, Feb. 16, 2016, https://www.nytimes.com/2016/02/17/world/middleeast/us-had-cyberattack-planned-if-iran-nuclear-negotiations-failed.html
https://en.wikipedia.org/wiki/Paul_M._Nakasone
https://en.wikipedia.org/wiki/Internet_Research_Agency
D.E. Sanger and N. Perlroth, U.S. Escalates Online Attacks on Russia’s Power Grid, New York Times, June 15, 2019, https://www.nytimes.com/2019/06/15/us/politics/trump-cyber-russia-grid.html
Cyber Warfare – Is Attack the Best Form of Defence?, https://www.gtlaw.com.au/insights/cyber-warfare-attack-best-form-defence
DoD Applies MAD Nuclear Doctrine to Cyber, The Lexington Park Leader, Aug. 5, 2015, https://lexleader.net/dod-applies-mad-nuclear-doctrine-to-cyber/
D. Paletta, U.S., China in Pact Over Cyberattacks That Steal Company Records, The Wall Street Journal, Sept. 25, 2015, https://www.wsj.com/articles/u-s-china-agree-over-cyberattacks-that-steal-company-records-1443205327
S. Waugh, Geneva Conventions for Cyber Warriors Long Overdue, National Defense Magazine, Mar. 18, 2020, https://www.nationaldefensemagazine.org/articles/2020/3/18/geneva-conventions-for-cyber-warriors-long-overdue
https://en.wikipedia.org/wiki/Geneva_Conventions
NATO Cooperative Cyber Defence Centre of Excellence, https://ccdcoe.org/
https://en.wikipedia.org/wiki/Tallinn_Manual
2015 UN GGE Report: Major Players Recommending Norms of Behaviour, Highlighting Aspects of International Law, https://ccdcoe.org/incyder-articles/2015-un-gge-report-major-players-recommending-norms-of-behaviour-highlighting-aspects-of-international-law/
An Updated Draft of the Code of Conduct Distributed in the United Nations – What’s New?, https://ccdcoe.org/incyder-articles/an-updated-draft-of-the-code-of-conduct-distributed-in-the-united-nations-whats-new/
Joint Statement on Advancing Responsible State Behavior in Cyberspace, https://www.state.gov/joint-statement-on-advancing-responsible-state-behavior-in-cyberspace/
https://www.csis.org/people/james-andrew-lewis
J.A. Lewis, Toward a More Coercive Cyber Strategy, Mar. 4, 2021, https://www.csis.org/analysis/toward-more-coercive-cyber-strategy
F. Bals, What Is a Software Bill of Materials?, https://www.synopsys.com/blogs/software-security/software-bill-of-materials-bom/
https://www.zero-day.cz/database/
C. Clancy and R. Ledgett, The US Must Adopt Software Bill of Materials to Thwart Cyberattacks, The Hill, Mar. 15, 2021, https://thehill.com/opinion/cybersecurity/543186-the-us-must-adopt-software-bill-of-materials-to-thwart-cyber-attacks?rl=1
C. Yanko, Using a Software Bill of Materials (SBOM) Is Going Mainstream, Security Boulevard, June 4, 2020, https://securityboulevard.com/2020/06/using-a-software-bill-of-materials-sbom-is-going-mainstream/
Cyber Supply Chain Management and Transparency Act of 2014, https://www.congress.gov/bill/113th-congress/house-bill/5793
D. Braue, Software ‘Bill of Materials’ to Become Standard?, https://ia.acs.org.au/article/2020/software-bill-of-materials-to-become-standard.html
https://www.cl.cam.ac.uk/research/security/ctsrd/cheri/
K. Nienhuis, et al., Rigorous Engineering for Hardware Security: Formal Modelling and Proof in the CHERI Design and Implementation Process, https://www.cl.cam.ac.uk/research/security/ctsrd/pdfs/202005oakland-cheri-formal.pdf
