February 28, 2023
Section IV. Illegal Activity Involving Cryptocurrency
The pseudonymity promised for cryptocurrency transactions has made them attractive from the start to criminals and others involved in illicit activities. It is not known precisely how much of the activity involving cryptocurrency and cryptographic methods is illegal, but the estimates shown in Fig. IV.1 suggest that billions of dollars worth of cryptocurrency are exchanged annually for illicit purposes. At present, when cryptocurrency is widely used for investment purposes, the fraction of illegal activity appears to be quite small; the crypto-world tracking company Chainalysis estimates that in 2021 only 0.15% of cryptocurrency transactions were for illegal purposes.
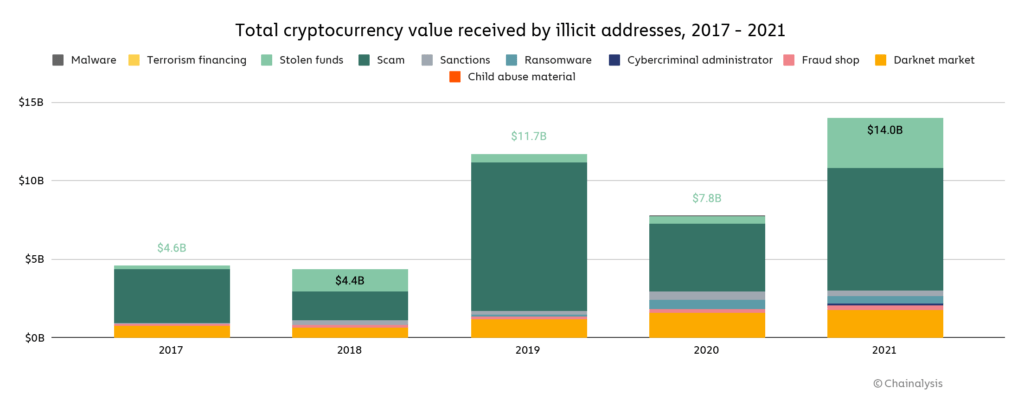
Figure IV.1. Chainalysis estimates of the total cryptocurrency value involved in illicit activities year-by-year from 2017 through 2021. The leading illicit activities are dark net purchases (gold band at the bottom), scams (sage green band near the top), and outright theft (light green band at the top). But other contributors include child pornography, fraud, ransomware, transactions violating sanctions, and financing for terrorism worldwide.
However, Fig. V.3 will show that a significant fraction of the cryptocurrency exchanges that have failed were because the site was engaged in illegal activity. For example, 9% of failed crypto exchanges were scams, and another 42% seem to have suddenly disappeared from the Web. In addition, another 5% of failed crypto exchanges involved massive hacks that stole their funds. Also, as we review in Sect. V of this post, there have been many anonymous sites on the Dark Web that were engaged in illegal activities. More recently, ransomware attacks have taken down Web sites, and the attackers have demanded payment in cryptocurrency, in return for providing programs that would restore data that was made inaccessible by the attack.
Figure IV.2 shows a computer screen of a user who has received a ransomware attack. It informs the user that their computer files have been encrypted. The user must either find a way to defeat the encryption (using frequent computer backups can sometimes allow the user to avoid paying the ransom to receive information to end the encryption), or they can pay the ransom; the most popular form of ransom has been to use cryptocurrency, on the assumption that the transaction cannot be traced.

Figure IV.2: The computer screen of the recipient of a ransomware attack. It informs users that their computer files have been encrypted. The user must either find a way to defeat the encryption (using frequent computer backups can sometimes allow the user to avoid paying the ransom to receive information to end the encryption), or pay the ransom, generally in cryptocurrency.
A great deal of time and effort has been expended by law enforcement officials and Web tracking companies, in order to identify the individuals who were engaged in illegal activity. In addition, companies have been formed that attempt to track down the sources of illegal payments. One of the goals of such companies is to locate and take down the main server for illegal transactions. Here we will review the history of efforts to trace the flow of cryptocurrency transactions for illegal purposes. Much of the material that we present is based on the 2022 book Tracers in the Dark by Andy Greenberg.
Sarah Meiklejohn was a graduate student in computer science at the University of California, San Diego (UCSD). In 2013, she began as part of her research project to purchase items from several Bitcoin exchanges. She converted dollars to Bitcoins and back again using a number of Bitcoin exchanges, and even conducted some business on Dark Web sites (without committing actual crimes). Meiklejohn subsequently noted the Bitcoin addresses she used and the address of the recipient or sender of her transactions. She was using the feature of the public blockchain system, where every blockchain transaction was visible to everyone using the system. Although one could look up every transaction on the blockchain, in order to discover the identity of the sender or recipient one would in principle have to know that person’s private key, and the private key was given by a long string of letters and numbers that could not be decoded by current algorithms.
Meiklejohn, however, used certain features of the Bitcoin blockchain to glean information about the transactions. For example, users could create a number of different “wallets,” each of which contained a certain amount of Bitcoin (and each had a secret private key). Imagine that a user purchased an item for 5 Bitcoin and used one wallet containing 2 Bitcoin and one containing 3 Bitcoin. The transaction would be listed on the blockchain as 2 Bitcoin from one address and 3 Bitcoin from a second address being moved to a single new address. Thus, Meiklejohn could deduce that the address with the 5 Bitcoin was the recipient, and that the 2 addresses with 2 and 3 Bitcoins belonged to the same sender.
Another feature of the Bitcoin system was that many early versions used a very specific method for making payments. Assume that one purchased an item for 3 Bitcoin using a wallet that contained 5 Bitcoin. The system would empty the 5-Bitcoin wallet and create 2 new wallets – a 3-Bitcoin wallet for the recipient and a new 2-Bitcoin wallet for the sender. If you searched through the blockchain, and found a previous transaction involving one wallet address, you knew that it had to be a 5-Bitcoin wallet associated with the purchaser (since both the 3-Bitcoin address going to the recipient and the 2-Bitcoin remainder going back to the sender had to be completely new addresses).
Using a supercomputer to search through the blockchain to identify clusters of wallet addresses, in many cases Meiklejohn was able to track an entire series of transactions back to individual senders and recipients. Sarah Meiklejohn began to collaborate with UCSD professors Stefan Savage and Geoffrey Voelker. They focused on well-known heists of large amounts of Bitcoin. By using the tracing techniques developed by Meiklejohn, they were able to trace the flow of Bitcoin to a small number of addresses where the stolen crypto was cashed out. In August 2013, they published a paper with the clever title “A Fistful of Bitcoins: Characterizing Payments Among Men with No Names.” In their conclusions they stated “We demonstrate that an agency with subpoena power would be well placed to identify who is paying money to whom. Indeed, we argue that the increasing dominance of a small number of Bitcoin institutions (most notably services that perform currency exchange), coupled with the public nature of transactions and our ability to label monetary flows to major institutions, ultimately makes Bitcoin unattractive for high-volume illicit use such as money laundering.”
Tracing Illegal Activity On the Blockchain:
As we have seen from articles such as Timothy May’s Crypto Anarchist Manifesto, at least some of the founders of blockchain technology envisioned that a number of users who were taking advantage of anonymity would be involved in illegal activities. Of course, what constitutes illegal activity can vary greatly from country to country; people who simply share their opinions with others could be in trouble in countries like North Korea, Iran or China. In the U.S., various illegal activities were undertaken using blockchain technology. This could constitute hiding assets so they would not be taxed, selling illegal drugs, activities such as child sexual abuse or sex trafficking, or ransomware attacks. In this section we will review some of the more infamous networks that were used for illegal purposes. We will review their history, the senior administrators of these networks, and we will discuss how their operations were uncovered by law enforcement personnel and closed down. Much of this section is based on information in Andy Greenberg’s book Tracers in the Dark: the Global Hunt for the Crime Lords of Cryptocurrency. Some of the material on the Silk Road anonymous online marketplace and its administrator, Ross Ulbricht, was gleaned from the 2017 book American Kingpin: The Epic Hunt for the Criminal Mastermind Behind the Silk Road, by Nick Bilton.
The Silk Road Anonymous Marketplace:
The first of these operations was the Silk Road Website on the Dark Web, one that catered to a number of illegal activities. The Silk Road site was established in 2011 by 27-year-old Ross Ulbricht, who operated his enterprise from San Francisco under the nickname Dread Pirate Roberts (a pseudonym taken from the movie The Princess Bride). The Silk Road was an anonymous marketplace. It offered a host of objects for sale – some of these were legal objects such as “apparel, art, books, cigarettes, erotica, jewellery, and writing services”. However, some 70% of the articles for sale on Silk Road were illegal drugs; this included “stimulants … opioids, ecstasy and dissociatives.” Figure IV.3 shows a page from the Silk Road online Web site with various drugs listed for sale. Federal authorities later estimated that between $30 million and $45 million were spent by 100,000 consumers on that site, in the two years of its existence. Since the transactions involved Bitcoin cryptocurrency and blockchain technology, buyers and sellers on Silk Road had reason to believe that their transactions were assured anonymity, as Ulbricht also assumed for himself.

Figure IV.3: A page displayed online on the Silk Road Marketplace Web site. A number of illegal drugs are listed for sale. Buyers paid for the merchandise using Bitcoin; it was assumed (incorrectly, as it turned out) that the blockchain technology guaranteed that the identity of the purchasers could not be determined.
The Texan and former physics major Ross Ulbricht was the facilitator of the Silk Road Dark Web site. In the early days of Silk Road, Ulbricht (using the pen name Dread Pirate Roberts or DPR) published a number of posts outlining his vision for the site. In his online posts, DPR considered the vendors on the Silk Road site to be a “community of heroes,” without whom citizens would be “swallowed by the nightmare reality of ever-expanding, all-powerful global oligarchy.” In various Web postings, DPR portrayed himself as the leader of a new frontier of personal freedom. “Now it is profitable to throw off one’s chains, with amazing crypto technology reducing the risk of doing so dramatically. How many niches have yet to be filled in the world of anonymous online markets? The opportunity to prosper and take part in a revolution of epic proportions is at our fingertips!”
Figure IV.4: Ross Ulbricht, the creator of the Silk Road Web anonymous marketplace, in 2011. Although the Silk Road site offered many different items for sale, some 70% of the Silk Road merchandise was illegal drugs, or unlicensed legal drugs.
Ross Ulbricht continued to post statements defending his activities and lauding the freedom and anonymity afforded by blockchain technology. Maintenance of the Silk Road Website was undertaken by a series of administrators around the globe. And the main servers for Silk Road were located in Reykjavik, Iceland. In the meantime, Ulbricht led a largely solitary life. Despite the fact that he had amassed millions in Bitcoin from his fees for the Silk Road activities, Ulbricht lived in an apartment in San Francisco that he had found on Craigslist; it cost him $1,250 a month. He hung around Internet cafes and public libraries in neighborhoods in San Francisco, where he supervised the Silk Road business using his laptop. He met girls by using online dating sites. His personal life could not be more different from our visual impression of a “drug kingpin.”
During the two years that the Silk Road site was online, Ulbricht made millions of dollars from purchases on this site. He tended to leave nearly all of it in online Bitcoin wallets. However, as the Silk Road site took off, he became more concerned about security for the site and for himself. He invested in strong encryption for his laptop. He procured some fake identities. He began to apply for citizenship in other countries where he thought he might be secure if he had to flee from prosecution. And he created a checklist of actions he could take to disappear if the “Feebs” (his term for the FBI) knocked on his door.
Ross Ulbricht became progressively more paranoid as the Silk Road flourished. After one year, the Silk Road was doing $500,000 per week in business. However, along with the success of the site, Ulbricht was experiencing ransomware attacks on various site locations and threats from competitors. A turning point occurred when one of the Silk Road vendors, a Utah man named Curtis Green, was caught in a cocaine bust. Ulbricht believed that Green had cheated Silk Road out of $350,000. Ulbricht worried that if the word got out that dealers could “stiff” the Silk Road, it could be fatal for his business. He mulled over possible actions to take against Green. He turned to an online seller who had represented himself as an experienced drug dealer. This person, who used the pseudonym Nob, asked Ulbricht “Do you want him beat up, shot, just paid a visit?” Eventually, Ulbricht decided that he needed to have Green killed.
Nob agreed to have Green killed in return for $80,000. When he received a photo of the dead Curtis Green, Ross paid off the killer. Unfortunately for Ulbricht, the “hit man” he contacted turned out to be an agent (actually a rogue agent seeking to profit himself) of the US Drug Enforcement Agency (DEA); anonymity is a double-edged sword. And the photo of the ‘hit’ was staged; Curtis Green was still very much alive. By this time, the Feds were closing in on ‘Dread Pirate Roberts.’ They claimed that an important clue was obtained from a coding error that Ulbricht had made, which pinpointed some of his postings as coming from a coffee shop in San Francisco. Once they had this IP address, they were able to deduce other information that led them to Ross Ulbricht. (Note: Some computer experts are skeptical of the government’s explanation for how they located Ross Ulbricht; they have speculated that agents may have used secret techniques to break into encrypted files. These computer specialists hypothesize that the government wants to maintain secrecy in order to protect their sources and the methods that they utilize in fighting crime. If the Feds had broken into Ulbright’s site without a warrant, they risked the possibility that their case against DPR might be thrown out for violating his Fourth Amendment rights.)
On Oct. 1, 2013, ‘Dread Pirate Roberts,’ the mastermind behind the Silk Road Dark Web marketplace, was captured by federal agents. In a scene right out of a ‘B’ movie, Ross Ulbricht was working on his laptop at a public library when he was disturbed by an altercation. A couple next to him broke out in an argument that appeared headed for violence. As Ulbricht turned to watch the couple, a woman sitting across from him snatched his open laptop, with access to the Silk Road administration site, and handed it to an associate. A couple of other people materialized, who grabbed Ulbricht and placed him in handcuffs. As it turned out, everyone in that same room with Ulbricht was an undercover federal agent.
All of these Byzantine maneuvers were deemed necessary to gain information on Ross Ulbricht. Although the Feds had determined that he was the operator of the Silk Road Dark Web site, they otherwise had little information regarding the details of the Silk Road enterprise. They hoped to extract this information from Ulbricht’s laptop; however, his laptop had been strongly encrypted so that once the cover was closed, it would be impossible for government officials to re-open it. The Feds hoped that Ulbricht’s computer would provide information on the Silk Road enterprise; and for that reason, they had to grab the laptop while it was still open. To make matters even more complex, at the time of his capture Ulbricht was discussing Silk Road matters with one of the top moderators of his Website. However, this ‘moderator’ was yet another federal agent, who had been tasked with keeping Ulbricht logged into the Silk Road site while he was apprehended by the agents.
The Feds hit the jackpot. Ulbricht’s laptop contained detailed records of the Silk Road: the sites on the Web; the amount of business done on the Silk Road; the IP addresses of site moderators; and Ulbricht’s own finances. His laptop had digital wallets containing Bitcoin worth millions of dollars, and back at his apartment he had flash drives with millions more in digital wallets. The apprehension of Ross Ulbricht was the result of a joint task force involving the FBI, the Internal Revenue Service (IRS), the Department of Homeland Security (DHS) and the Department of Justice (DOJ). Locating and capturing Dread Pirate Roberts involved a collaborative effort among many different federal agencies. And where was this criminal mastermind when he was picked up by the Feds? He was working at a table in the public library in the Glen Park neighborhood of San Francisco!

Figure IV.5: The day after Ross Ulbricht was captured by federal agents, the various federal agencies that collaborated on his capture posted this message: THIS HIDDEN SITE HAS BEEN SEIZED. After that the Silk Road site was taken down.
After his capture, Ross Ulbricht was charged with money laundering, computer hacking, conspiracy to traffic narcotics, and murder for hire. However, although Ulbricht had paid $730,000 to hire hit men, no one was ever murdered, and eventually the murder for hire charges were dropped. However, Ulbricht was convicted on all five of the remaining counts in the federal indictment. Prior to sentencing, Ulbricht defended his actions as being motivated by a desire to ensure that people could keep their personal interactions private. “I wanted to empower people to make choices in their lives for themselves and to have privacy and anonymity … I am not a self-centered sociopathic person that was trying to express some, like, inner badness. I just made some very serious mistakes.” Federal judge Katherine Forrest, reading from Ulbricht’s own chat logs, showed that he had been unrepentant about dealing dangerous drugs and had been willing to order the murders of people he thought had cheated him. She sentenced Ross Ulbricht to two concurrent life sentences in prison without the possibility of parole. Ulbricht’s appeals have been denied, and today he is incarcerated in a maximum-security prison in Arizona.
In one final bizarre twist to the Silk Road saga, it turned out that two federal agents, who had been working on tracking down Silk Road transactions in attempts to penetrate the Silk Road hierarchy and locate the kingpin of the entire Website, had themselves looted vast sums of Bitcoin from the Silk Road site. Carl Force was a DEA agent who had managed to contact Ross Ulbricht online using various pseudonyms. In fact, Force was the character ‘Nob’ who had negotiated with Ulbricht regarding a hit on Silk Road moderator Curtis Green. And it was Force, and not Green, who had cheated Ulbricht out of $350,000. Force also admitted to stealing $370,000 from a customer of CoinMKT; Force was working for that company while moonlighting from his DEA job. After pleading guilty to the charges against him, Force was sentenced to 78 months in federal prison.
A second crooked agent was Shaun Bridges, a former Secret Service agent who had been assigned to the multi-agency Baltimore Silk Road Task Force. As part of his job, Bridges conducted forensic computer investigations in order to identify people who were committing crimes on the Silk Road site. Bridges was also searching for ‘Dread Pirate Roberts,’ the founder of Silk Road. In Jan. 2013, Bridges broke into a Silk Road administrator’s account and moved Bitcoin worth $820,000 into digital wallets that he controlled. Bridges pled guilty and was sentenced to five years in federal prison. Although both Bridges and Force were members of the Baltimore Silk Road Task Force, there is no evidence that they coordinated their illegal actions.
Chainalysis: Deciphering Transactions on the Blockchain:
One of the initial claims of the founders of blockchain technology was that the identity of the users of cryptocurrency could never be determined. In addition to the public information available on the blockchain, the identity of the user could only be obtained using a private key, which only the user possessed, and the private key could not be deciphered using current techniques. So, companies or federal agents wishing to track down people engaged in illegal activity using cryptocurrency seemed to be facing impossible odds of tracking the money and the illegal goods. However, computer specialists began to spend a great deal of time and creativity in attempts to make the blockchain “transparent.” We will review the efforts to “trace the untraceable,” namely to decode transactions on the blockchain. We will focus on the work of Chainalysis, the most successful company to date in this enterprise.
The founders of Chainalysis were Matthew Gronager, a Danish physicist and computer specialist, a second Danish computer scientist named Jens Møller, and South African economist Jonathan Levin. Earlier in his career, Gronager had used his expertise in computer programming to create a “pod” of PCs to solve quantum physics problems. He subsequently headed up a group of computer scientists who were managing “farms” of computers to store and analyze massive amounts of data at the European Centre for Nuclear Research, CERN, in Geneva, Switzerland. At that time the CERN Large Hadron Collider was searching for the Higgs Boson, and they were managing exceptionally large amounts of data. However, when Gronager first became aware of the development of Bitcoin technology, he quit his job and founded a Bitcoin exchange called Kraken.
Gronager found the technology behind the blockchain to be extremely ‘sweet,’ and he understood that the ability to conduct transactions with no third-party intermediaries such as bankers or lawyers was truly revolutionary. At the same time, he felt that the appeal of blockchain technology to crypto-anarchists, and their advocacy of using the blockchain for even illegal purposes, was misguided. Gronager believed that a great advantage of blockchain technology was that it was transparent, namely that anyone could locate any transaction on the blockchain, even if they could not identify the user involved. Initially, Gronager began investigating the blockchain in an effort to determine who had made off with 850,000 Bitcoins in the hack of the Mt. Gox Bitcoin exchange, which we review in Sect. V.
Gronager began his work with Chainalysis by using techniques for tracing and connecting blockchain transactions that had been outlined by Meiklejohn and collaborators, and described earlier in this Section. Gronager combined this with his skill as a computer scientist to greatly increase the speed with which links could be combined, and the speed at which queries about individual transactions could be investigated. In addition, Gronager and Møller established hundreds of their own nodes on the Bitcoin network. These nodes collected information on the IP addresses of users who were initiating transactions. In this way they could construct a “map” of the IP addresses of servers involved in blockchain transactions. Eventually, Chainalysis was able to determine the flow of currency through the information recorded on the blockchain, which was available for anyone to see. Figure IV.6 shows a schematic picture of how Chainalysis can track transactions on the Dark Web. Funds from a Darknet transaction are channeled through a bridge to two different cryptocurrencies, Bitcoin and Ethereum. Chainalysis’ Reactor program has the ability to follow the funds, and to determine where they are stored and when they are converted into traditional currency.
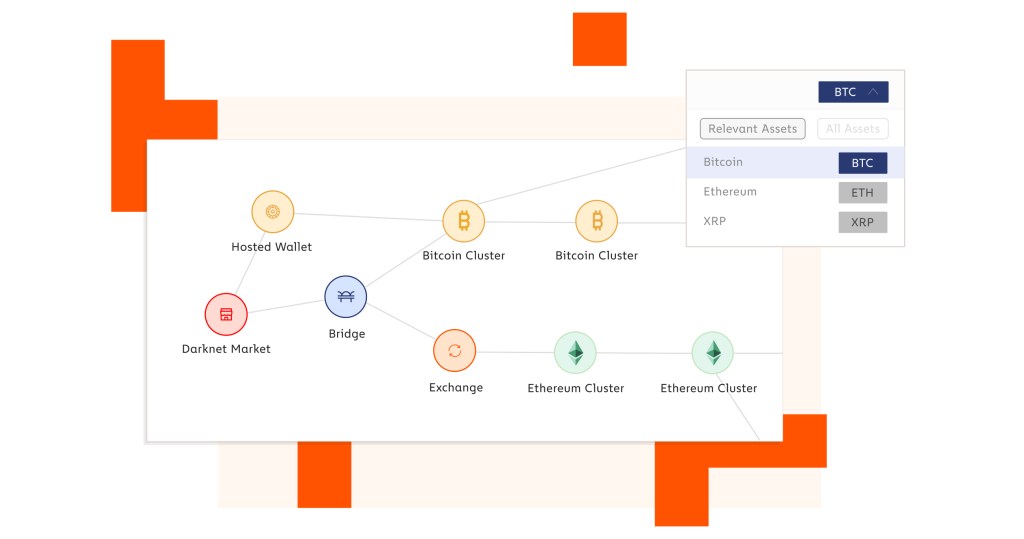
Figure IV.6: Schematic showing how Reactor, a program developed by the blockchain tracking company Chainalysis, can track transactions that use cryptocurrency. In this picture, a transaction takes place on the Dark Web. The payments are split into two different cryptocurrencies. The Reactor program is able to track those funds and to analyze where they are stored or converted into traditional currencies.
Gronager was convinced that the permanence and visibility of blockchain transactions was a great feature of this new technology. This enabled his company Chainalysis to follow sequences of transactions, and eventually determine the location of the server on which the transactions were based, and in many cases pinpoint the user (who had assumed his or her identity could not be traced). Chainalysis tried to sell their technology to banks and money-managing firms. However, these firms were convinced that the only use for the new blockchain technology was for criminal purposes, so Chainalysis failed to recruit them as customers. However, Chainalysis found immediate clients in law enforcement. Agencies such as the FBI, CIA, the Department of Justice, and the IRS all expressed interest in the findings of Chainalysis.
Matthew Gronager continued his quest to determine the identity of the thief or thieves who had looted Bitcoin from the Mt. Gox exchange. Eventually, he discovered that for a while, the stolen Bitcoin had been cashed out using an exchange called Trade Hill. However, at some point the administrators at Trade Hill became suspicious about the enormous volume of Bitcoin, and the thieves had to turn to other exchanges. Eventually, Gronager discovered that the Bitcoin was being cashed out at a cryptocurrency exchange called BTC-e. The BTC-e exchange appeared to be a site that was extremely attractive to crypto hackers, presumably because the exchange had no protections to avoid being used for criminal activity. In fact, BTC-e had become a “go-to” site used by the perpetrators of ransomware. An IRS agent called Tigran Gambaryan, using Chainalysis techniques, discovered that the person who had cashed out the stolen Mt. Gox Bitcoins was one of the top administrators of BTC-e. This led to the conclusion that perhaps the BTC-e exchange was created specifically to cash out the proceeds from illegal activities. And the username of the Mt. Gox hack perpetrator became known – WME.
Eventually, federal agents were able to track down WME from activity several years earlier involving stolen credit card numbers. They determined that the Mt. Gox hacker was Russian Alexander Vinnik. That information alone was not particularly useful, since the Russians do not extradite criminals to the West. As long as Vinnik remained in Russia, he was safe from Western authorities. However, in 2017 agents learned that Vinnik was on a vacation in Greece. He was arrested there; in addition, Chainalysis had determined the location of the main BTC-e servers. After seizing those servers, agents were able to extract the usernames and IP addresses of a host of users who were involved in illegal activities.
Today, Chainalysis is a large corporation that specializes in tracing and analyzing transactions on the blockchain. They have continued their operations, namely the tracing of blockchain transactions and identification of the IP addresses and names of users of cryptographic methods to obscure illegal activity. In addition, Chainalysis maintains a number of nodes on the blockchain, and from those nodes it gathers information on the location of servers involved in the cryptocurrency trade. However, Chainalysis has also developed a number of new techniques for extracting information from the blockchain. The precise methods are now company secrets, so outsiders can only guess at the current methods being used to decipher blockchain technology.
Chainalysis’ own publicity materials provide some hints regarding their surveillance techniques. First, Chainalysis purchased an early blockchain tool called WalletExplorer. Various individuals involved in criminal activities on the Dark Web used WalletExplorer to see if their transactions were traceable. But WalletExplorer recorded the IP addresses of the search requests, and it sent those addresses to Chainalysis. Next, a tool called Simple Payment Verification allowed users to store small bits of the blockchain to track their purchases. Once again, that service allows agencies to extract not only the IP address of the recipient, but also all of their blockchain addresses. Chainalysis uses this information in their tool Orlando. And finally, Chainalysis has produced a tool called Rumker. This product allows Chainalysis to utilize information collected from their Bitcoin nodes to identify users who don’t use the Tor network to scramble their transactions but instead run them on the unscrambled ‘clearnet.’
In early 2022, Chainalysis had raised enough capital that its valuation was listed at $8.6 billion. Its customers included law enforcement agencies around the world, in addition to contracts from several countries. Chainalysis techniques had been instrumental in taking down Dark Web anonymous marketplaces such as Silk Road and AlphaBay; and we will show that it was also an essential contributor to the effort that took down Welcome to Video, a world-wide Web site that collected and disseminated child sexual abuse materials. Nevertheless, despite the success of Chainalysis in stopping these illegal activities, the work of Chainalysis has been controversial. For example, Alex Gladstein of the global civil liberties group Human Rights Foundation, has stated that “I think they’re terribly bad people … it’s not just encrypted communications that we need to protect ourselves and to protect our democracy, but also private money … I think that spying on people is the tactic of tyrants. And I think that democratic societies should find other ways of solving crime that don’t involve warrantless surveillance.”
To support his statements, Gladstein pointed to the work of the Belarus Solidarity Foundation, which raised funds in Bitcoin that were used to support workers who opposed that country’s strongman Alexander Lukashenko. Gladstein also mentioned that Ukrainian groups fighting against Vladimir Putin’s invasion had raised millions of dollars in cryptocurrency donations to fund the resistance. He also pointed to the potential for encrypted transactions for groups like the Uighurs and the Hong Kong resistance in China, as encrypted communications might provide those citizens with means to avoid detection by the repressive government of Xi Jinping. And Gladstein pointed to the fact that Chainalysis had recently signed contracts with countries in the Middle East that had dubious records on human rights. However, the world has learned the hard way that computer records are seldom secure; if they are accessible to hackers, one should also assume that they are accessible to “warrantless surveillance” by law enforcement and repressive governments. There can be no absolute right to blockchain privacy; the victims and potential victims of cryptocurrency-fueled crime also have rights that must be considered.
Welcome To Video: Child Sexual Abuse Material Adopts Blockchain
In 2017, IRS agents who were investigating a Dark Web organization called AlphaBay, a successor to the Silk Road anonymous marketplace, had traveled to Bangkok, Thailand to arrest the major coordinator of that organization. While in Thailand, they talked with Chainalysis administrator Jonathan Levin to discuss potential future targets who were using blockchain techniques to finance illegal activities. Levin suggested to them that they consider a Dark Web outfit that was involved in producing and sharing child sexual abuse materials (CSAM) and financing the operation through cryptocurrency transactions. The name of the site was Welcome to Video (WTV). According to Levin, the site appeared to be the largest CSAM operation ever seen, and the epicenter of its operations appeared to be South Korea.
When Chainalysis and the IRS-CI (Criminal Investigation) team investigated Welcome to Video, they were surprised that the site was unsophisticated with respect to hiding their servers and transactions. Where sites such as AlphaBay had employed intermediary addresses to hide their monetary trail, or processed their transactions through “mixers” that would deliberately obscure the relations between users, Welcome to Video had used none of these sophisticated methods. It was relatively easy for computer investigators to trace the chain of events. Furthermore, investigators could trace the contents of digital wallets where they were converted into traditional currency at a very small number of cryptocurrency exchanges, notably Bithumb and Coinone in South Korea and Huobi in China.
With respect to child sexual abuse materials, the use of cryptocurrency represented a major change in the handling of CSAM pictures and videos. Prior to Welcome to Video, much of the traffic in child pornography involved pedophiles swapping materials with others. Because no currency was involved in these transactions, law enforcement officials could catch individuals or small groups, but they were unable to round up large numbers of offenders. However, the WTV operation represented a major escalation in child pornography. First, the volume of material on this site was unprecedented – more than 250,000 videos were available here. Next, the WTV site offered its viewers incentives; in addition to paying in Bitcoin for watching videos, users could upload their own child pornography. They would obtain “points” based on the number of people who viewed their material. Thus, the operators of the WTV site were encouraging pedophiles to produce and upload their own material.

Figure IV.7: A schematic depicting the Welcome to Video site on the Dark Web. Visitors to this site could use cryptocurrency to view hundreds of thousands of video clips of child sexual abuse. The site was taken down by a multi-country task force, and in 2017 the administrator of the site was jailed in South Korea.
Because the Welcome to Video site provided a clear money trail through the blockchain, the IRS decided to pursue transactions on this site, rather than agencies such as FBI and Homeland Security that had traditionally investigated child sexual abuse cases. In fall 2017, the IRS created a team of agents to track the flow of funds, to identify and prosecute the mastermind behind WTV, and to arrest and prosecute sexual abusers of children. To access Welcome to Video, IRS agents created accounts and passwords, and logged into the site. The agents were experienced in tracking down Dark Web sites such as the Silk Road, and their work had concentrated on illegal activity such as drug dealing. However, the materials on the WTV site were deeply shocking to the IRS team. First, the agents were stunned to see the incredible number of videos on the site. Also, agents had expected to find material featuring pre-teen and teenage children. However, to their horror they found extensive materials that involved young children, even toddlers on the site. The agents found that viewing these materials left them with deep psychic scars – these videos could not be “un-viewed” once they had seen them.
Although the child sexual abuse materials were horrible, in terms of tracing the materials and discovering the location of the main server for the site, the situation was straightforward. Investigators found that each video on the site contained inside the HTML the IP address of the main server. Although the videos had been encrypted using the Tor Project multi-layered system, the videos themselves contained a link back to the main server. It appeared that all of the material was being stored on a computer belonging to a 21-year-old Korean named Son Jong-woo.
At this point, the IRS agents added a U.S. attorney who specialized in child exploitation. In addition, they partnered with investigators from Homeland Security. The DHS investigators had developed a rapport with the Korean National Police Agency. This connection would prove essential since the KNPA had a reputation for being difficult to work with. They also teamed up with a staffer from Chainalysis who used his company’s Reactor program to trace transactions through the Bitcoin blockchain. Tracing the links in this system turned out to be much simpler than the AlphaBay online marketplace, where the levels of encryption were much more stringent than in Welcome to Video. Not only did the investigators find multiple links to the WTV administrator Son Jong-woo, but they were able to identify hundreds of consumers who had been viewing or uploading child sexual abuse videos.

Figure IV.8: After the Welcome to Video site was taken down by a multi-national task force by the United Kingdom, U.S., Germany and the Republic of Korea, users logging in found this notice on that Dark Web site.
The suspects, nearly all of whom were men, were located around the world. The only thing they had in common was their depravity. They came from all races, ages, and professions. In particular, the IRS-CI agents focused on a few American pedophiles. The first active case was a former Congressional staff member who was now working for an environmental organization. He lived right in the heart of the District of Columbia. The agents found that this man was returning to the States from a trip to the Philippines, which was a haven for sex tourists with an interest in children. When the man returned to the U.S., customs officials detained him and confiscated his laptop and cell phone to search for evidence. The computer contained videos showing both child sexual exploitation, and videos of adult sexual behavior that had been secretly recorded. However, when the agents came to arrest the man, they found that he had committed suicide.
A second case involved a man who was an assistant principal of a high school in Georgia. When the man was questioned, he admitted to paying for materials on the Welcome to Video site, but in addition acknowledged that he had sexually abused some students at his school. A third target turned out to be a Border Patrol agent in Texas; this was disturbing to the investigating agents, who themselves were employees of Homeland Security. Even more disturbing was the fact that the Border Patrol agent had uploaded videos of his own stepdaughter being sexually assaulted. The agents visited the man, separated him from his stepdaughter, and interviewed them; both of them confirmed the sexual abuse.
The Welcome to Video case expanded to involve investigators from other countries. The National Crime Agency in the U.K. sent agents to Korea, where they were joined by agents from the German federal police. In February 2018, Korean officials arrested Son Jong-woo as he returned home from a trip. They found a PC in his bedroom that contained all the Welcome to Video materials. Remarkably, Son had not encrypted the materials on his computer, which contained the WTV videos, a user database, and all of the digital wallets that contained Son’s Bitcoins. The U.S. agents extracted a copy of the Welcome to Video databases, and they produced a “look-alike” Welcome to Video site. This enabled them to construct a directory of the WTV users, which they used to trace their cryptocurrency transactions.
The team then began to prosecute the users of this child pornography site. The highest priority was those who had produced their own child sexual abuse videos; next was people who had uploaded videos produced by others; and the final category was people who viewed the videos. Eventually, 337 people were arrested by authorities over the world, and 23 children were removed from sexually abusive situations. The methods for tracing blockchain transactions had allowed the authorities to shut down the world’s largest collection of child sexual abuse materials. However, in July 2020 Son Jong-woo was released from a Korean prison after serving an 18-month sentence for his role in uploading child sexual abuse materials. U.S. authorities had urged that Korea extradite Son to the U.S., but their request was denied. The light sentence was shocking; however, it sparked significant outrage in Korea. As a result, legislation was introduced by Korea’s National Assembly to increase punishments for uploading or downloading CSAM materials.
The Continuing Dark Web Sector
The ability of worldwide law enforcement agencies to trace the users and co-ordinators of Dark Web sites, using Chainalysis software products, has not deterred new sites popping up in the wake of ones shut down, to service continuing demand for drug sales, money laundering, information stolen in computer hacks, etc. Figure IV.9 shows Chainalysis results for the still growing darknet revenue. However, the illicit revenue has not grown as rapidly as total cryptocurrency transaction volume, as indicated by the dwindling darknet market share represented by the yellow curve in Fig. IV.9.
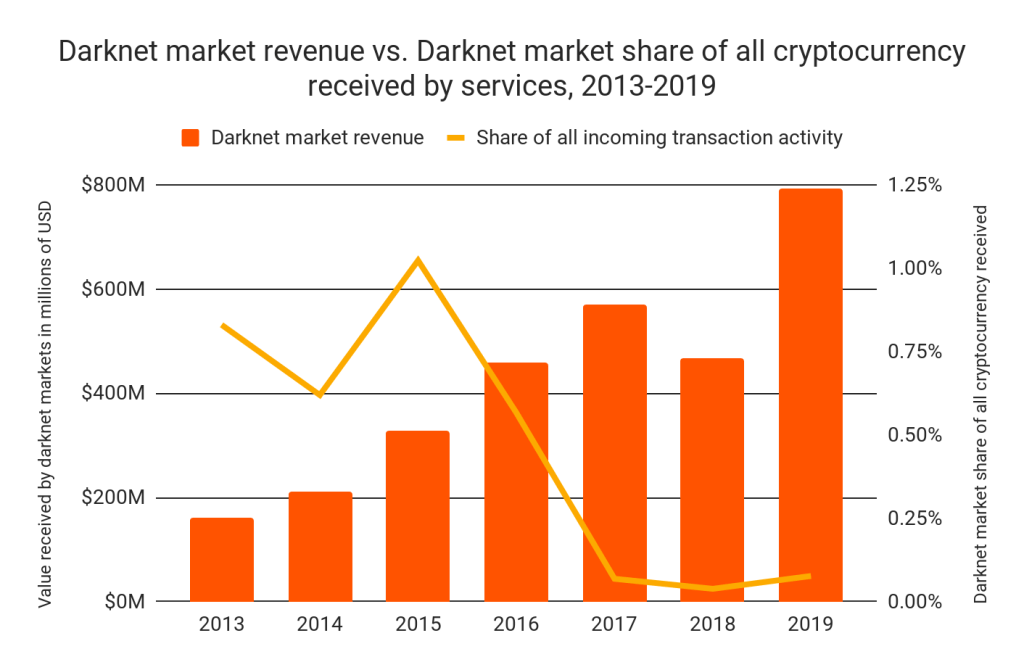
Figure IV.9. Chainalysis estimates for the total cryptocurrency revenue associated with Dark Web sites, year by year, and for the share of all crypto transaction volume that the Dark Web activity represents.
Figure IV.10 shows the major sites involved in crypto-fueled Dark Web activities and their share of the total Dark Web market as a function of time. When the dominant site AlphaBay was shut down by the authorities in 2017, its Russia-based competitor Hydra expanded to take up the displaced volume. By early 2022 Hydra was capturing more than 90% of all economic value in the darknet market ecosystem. But the Hydra marketplace was, in turn, shut down in April 2022 by a joint U.S.-German law enforcement operation, and new competitors are now vying for its market share. The figure also reveals that Dark Web legacy site names are sometimes rebooted, with new ownership, after previous failures; thus, Silk Road 3.1 was, until its recent shutdown, one of the continuing illicit drug-sale dominated Dark Web sites. Even armed with Chainalysis’ powerful blockchain tracing resources, law enforcement faces continuing challenges to monitor and halt crypto crime.
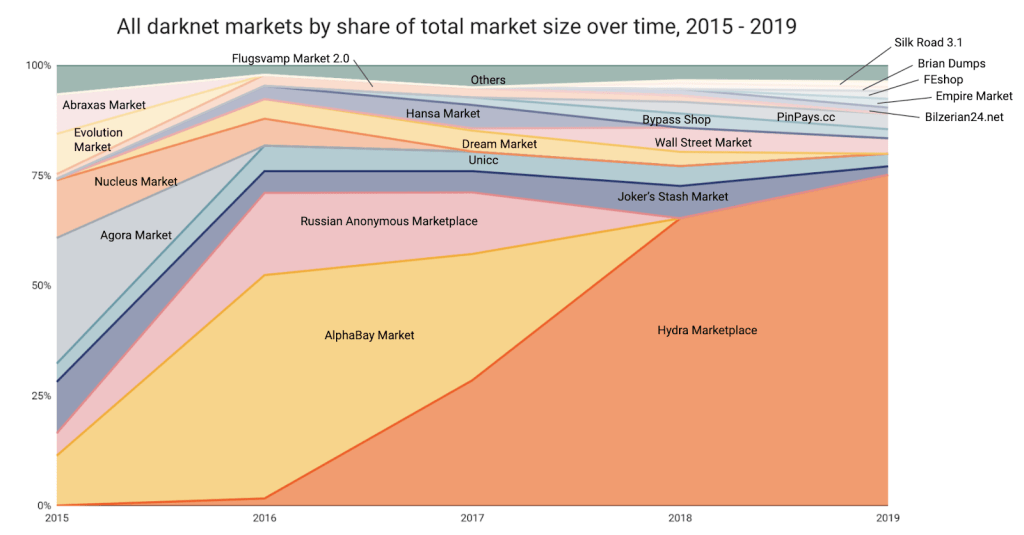
Figure IV.10. The major Dark Web sites involved in cryptocurrency-fueled illicit activities, and the evolution of their market shares over time from 2015 to 2019.
— To be continued in Part III —
